There are two options how to suppress Windows 10 forced updates; either disable privileged scheduled tasks which run at System account, or block their access to needed services by permissions. Both ways are not so easy:
1. You can disable/modify privileged scheduled tasks if you act as System account too. To do this, you have to use freeware PsExec utility from Sysinternals (unzip PsUtils tools somewhere in your Path).
1a) To run Scheduled Tasks snap-in as System account, type at the Elevated Command Prompt:
psexec -i -d -s mmc taskschd.msc
and then you can disable following three tasks interactively in GUI
1b) To disable affected scheduled tasks directly from commandline, type:
psexec -i -d -s schtasks /change /tn "microsoft\windows\updateorchestrator\schedule scan" /disable
psexec -i -d -s schtasks /change /tn "microsoft\windows\windowsupdate\scheduled start" /disable
psexec -i -d -s schtasks /change /tn "microsoft\windows\WaaSMedic\PerformRemediation" /disable
To revert those scheduled tasks back, type:
psexec -i -d -s schtasks /change /tn "microsoft\windows\updateorchestrator\schedule scan" /enable
psexec -i -d -s schtasks /change /tn "microsoft\windows\windowsupdate\scheduled start" /enable
psexec -i -d -s schtasks /change /tn "microsoft\windows\WaaSMedic\PerformRemediation" /enable
These commands may be also run from CMD batch file. Kiitos to TairikuOkami for identifying the 3rd service.
2. Different approach is to block access of System account to underlying services; so the mentioned tasks cannot neither start nor modify them. You may use freeware utilities from Helge Klein.
2a) To block System account access to services interactively:
- install SetACL Studio, run it, enter product key from download page, from menu View select Detailed
- expand Services node, select Windows Update entry
- to change ownership, in right pane click Select, click Advanced, click Find now, select Administrators, click OK
- click on Save button
- in right pane click to Add (it creates new Access Control Entry for service)
- click Advanced, click Find now, select System, click OK
- at newly added line, click on Allow symbol in Type column to change type of Access Control Entry from Allow to Deny
- at the same line, click in Permissions column
- select the following permissions: Change configuration, Start, Stop, Delete, Change permissions, Take ownership
- click on Save button again; System account now cannot manipulate this service
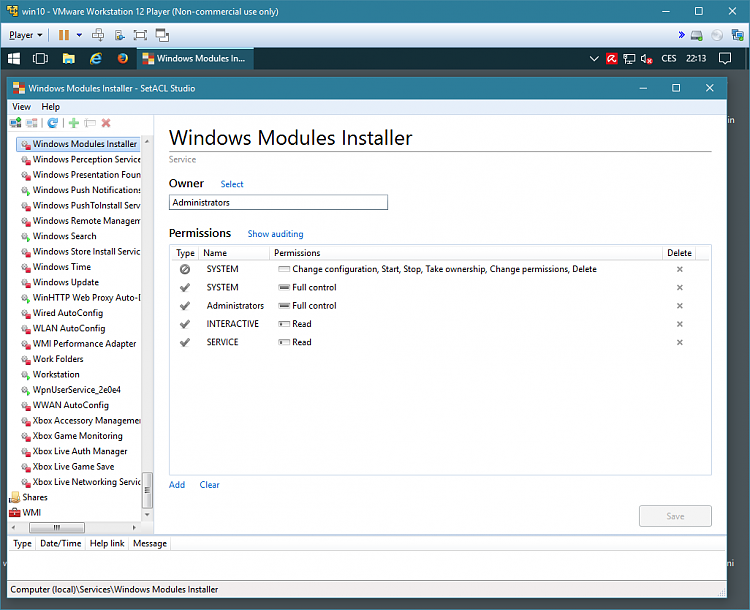
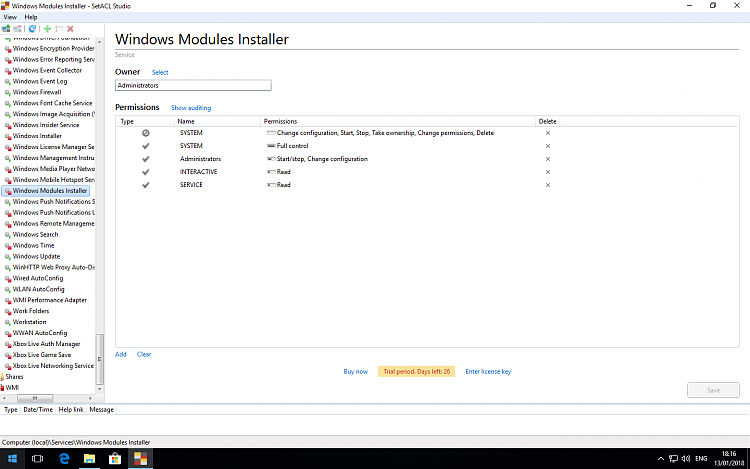
- repeat the same steps as above for Windows Modules Installer service
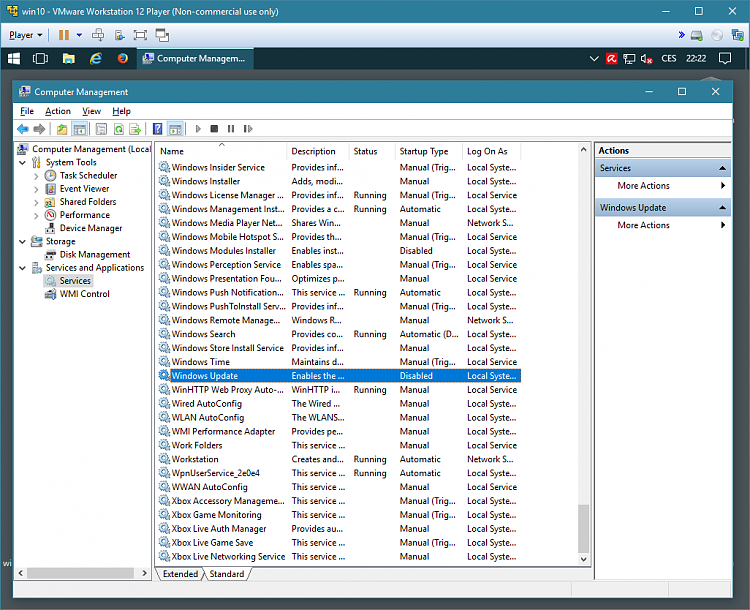
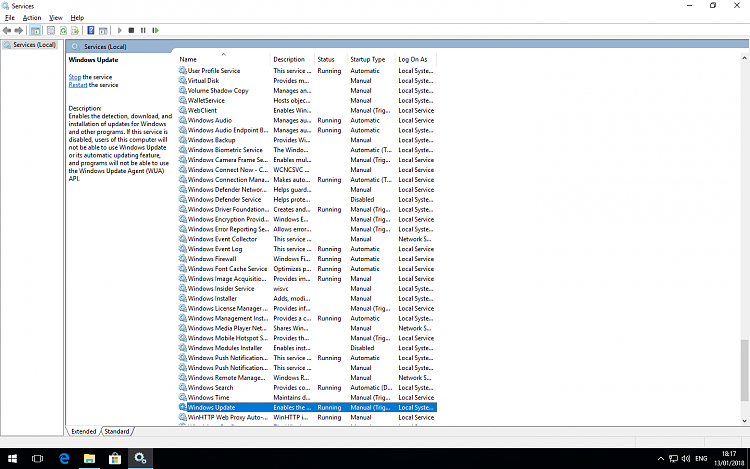
- using regular Services snap-in in MMC console, set both mentioned services to Disabled.
You need to modify two services this way: wuauserv (Windows Update) and TrustedInstaller (Windows Modules Installer, the name depends on language). All three steps are necessary: setting Administrators as service owner, setting six Deny permissions for System, and disabling the service.
To revert to normal state, in SetACL Studio simply click Deny symbol (it changes to Allow) and Save, then set service start type to Manual in Services snap-in. Do these steps for both services.
2b) To block System account access to services from elevated command line or from CMD batch file:
- download SetACL utility from Helge Klein website, place it on your Path
- test it using commands:
setacl -on "wuauserv" -ot srv -actn list
setacl -on "trustedinstaller" -ot srv -actn list
- change owner using commands:
setacl -on "wuauserv" -ot srv -actn setowner -ownr "n:Administrators"
setacl -on "trustedinstaller" -ot srv -actn setowner -ownr "n:Administrators"
- set blocking ACE entries:
setacl -on "wuauserv" -ot srv -actn trustee -trst "n1:system;ta:remtrst;w:dacl"
setacl -on "wuauserv" -ot srv -actn ace -ace "n:system;p:full;m:grant;w:dacl"
setacl -on "wuauserv" -ot srv -actn ace -ace "n:system;p:SERVICE_CHANGE_CONFIG,SERVICE_START,SERVICE_STOP,WRITE_OWNER,WRITE_DAC,DELETE;m:deny;w:d acl"
sc config wuauserv start=disabled
setacl -on "trustedinstaller" -ot srv -actn trustee -trst "n1:system;ta:remtrst;w:dacl"
setacl -on "trustedinstaller" -ot srv -actn ace -ace "n:system;p:full;m:grant;w:dacl"
setacl -on "trustedinstaller" -ot srv -actn ace -ace "n:system;p:SERVICE_CHANGE_CONFIG,SERVICE_START,SERVICE_STOP,WRITE_OWNER,WRITE_DAC,DELETE;m:deny;w:d acl"
sc config trustedinstaller start=disabled
...please treat two strings "d acl" as "dacl", forum formats long lines erratically
- delete blocking ACE entries for allowing Windows Update temporarily:
setacl -on "wuauserv" -ot srv -actn trustee -trst "n1:system;ta:remtrst;w:dacl"
setacl -on "wuauserv" -ot srv -actn ace -ace "n:system;p:full;m:grant;w:dacl"
sc config wuauserv start=demand
setacl -on "trustedinstaller" -ot srv -actn trustee -trst "n1:system;ta:remtrst;w:dacl"
setacl -on "trustedinstaller" -ot srv -actn ace -ace "n:system;p:full;m:grant;w:dacl"
sc config trustedinstaller start=demand
3. Recommended workflow, i.e. How to survive periodic patch parties:
Once a month (probably after Black Tuesday) it is proper to patch Windows systems in a controlled way. It is relatively simple but time consuming activity:
- image system partition(s) using Macrium Reflect Free, or at least create Restore Point
- unblock Windows Update mechanism according to blocking method used (enable scheduled tasks, or clear Deny permissions and set services to Manual start)
- run wushowhide.diagcab immediately to block unwanted patches and drivers
- run Windows Update
- revert Windows Update back to blocked state
- image system partition(s) again.
That's all, for now. And, of course, many thanks sent to Redmond with love.
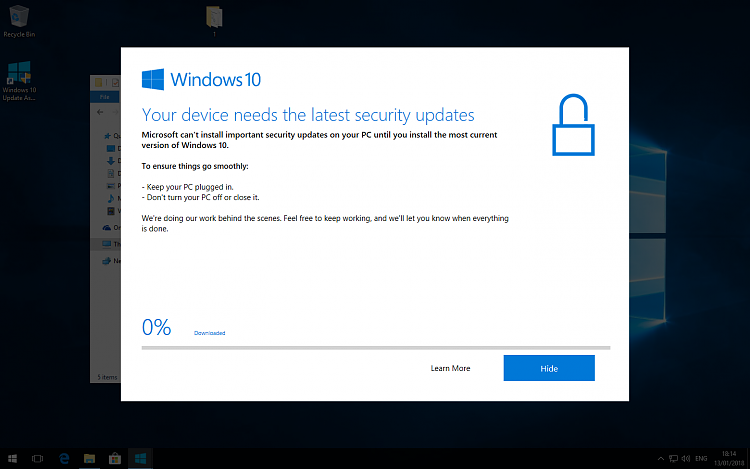
windows is still pushing drivers updates i dont want, and it does not matter how many times i disable that stupid service. Nothing is working and windows is completely ignoring that i NEED APPROVED drivers from MANUFACTURER otherwise my OS is bricked with blackscreen and BSOD problems until I reinstall it again. This problem lasts for around week and half and I must reinstall those drivers every day again and again, because Im not able to stop those stupid updates.


 Quote
Quote