New
#210
Cumulative Update KB4482887 Windows 10 v1809 Build 17763.348 - March 1 Win Update
-
-
New #211
-
New #212
-
New #213
@IronZorg89
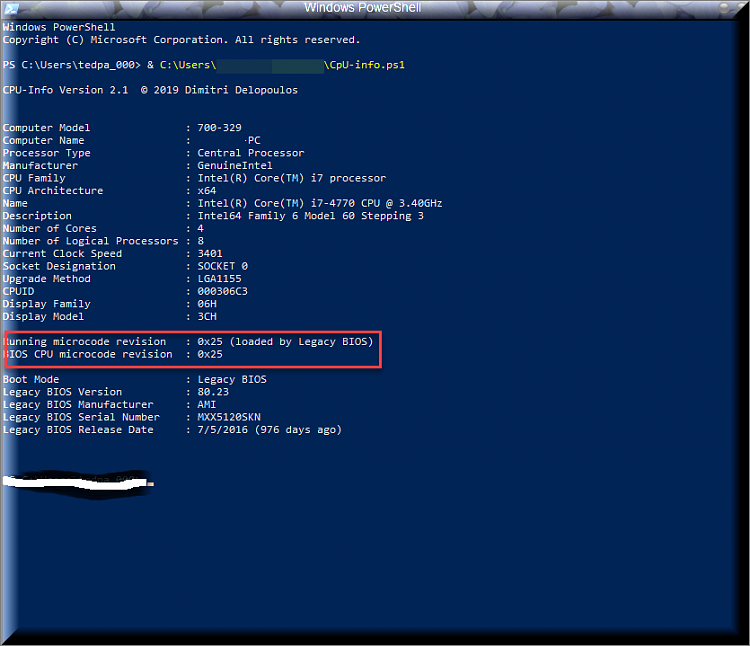
You installed KB4465065 now you have microcode 25 and l1 protection flashed enabled.
nice so my post had a value afterall, i think :)
-
New #214
Hardware support for branch target injection mitigation is not required to enable Reptoline on a Linux machine. You can, for example, enable Retpoline on a system with Core 2 Duo or a Core 2 Quad. And I had Retpoline enabled on a Linux machine months before I updated the CPU microcode.
But according to the Microsoft article linked to in the original post,
Since Retpoline is a performance optimization for Spectre Variant 2, it requires that hardware and OS support for branch target injection to be present and enabled.
Either that's a false statement, or the implementation of Retpoline in the Linux Kernel is different from the implementation of Retpoline in the Windows kernel.
-
New #215
There is something wrong here!
Once you run KB4465065 it updates the Running microcode revision not the BIOS/UEFI one. The KB4465065 does not touch BIOS/UEFI...
How come it changed in both?
According to your previous image (before updating KB4465065), after the update you should have:
Running microcode revision : 0x25 (loaded by Windows 10)
UEFI CPU microcode revision : 0x24
-
New #216
Maybe your script has a bug?
-
-
New #218
-
-
New #219
No problem :)
Related Discussions



 Quote
Quote