New
#50
Protect your Windows devices against Spectre and Meltdown
-
-
-
New #52
To get the white papers on Meltdown & Spectre(and tons more technical information on the subject): Meltdown and Spectre
Meltdown
Meltdown breaks the most fundamental isolation between user applications and the operating system. This attack allows a program to access the memory, and thus also the secrets, of other programs and the operating system.
If your computer has a vulnerable processor and runs an unpatched operating system, it is not safe to work with sensitive information without the chance of leaking the information. This applies both to personal computers as well as cloud infrastructure. Luckily, there are software patches against Meltdown.
Spectre
Spectre breaks the isolation between different applications. It allows an attacker to trick error-free programs, which follow best practices, into leaking their secrets. In fact, the safety checks of said best practices actually increase the attack surface and may make applications more susceptible to Spectre
Spectre is harder to exploit than Meltdown, but it is also harder to mitigate. However, it is possible to prevent specific known exploits based on Spectre through software patches.
-
New #53
The timing of the whole Meltdown/Spectre thing is peculiar. The major players were alerted to the vulnerability in June 2017 and after discussion decided that they would announce the problem on January 9, 2018. Probably with the notion that it would get lost in the noise from CES. So here's a conspiracy theory... ;-)
Intel and AMD had considerable time to study the 3 vulnerabilities and figure out how their processors would be affected. AMD thought the impact on their processors would be minimal, withess their inital pronouncement when the news broke early. Intel realized Meltdown mitigation would have more of an impact on their processors than on AMD's so they decided to suggest a Meltdown fix to be applied to both Intel and AMD processors. Tom Lendacky, the Linux guy at AMD, figured this out and wrote a memo on December 26, 2017 stating that AMD processors were not vulnerable to Meltdown and should not have this fix applied: LKML: Tom Lendacky: [PATCH] x86/cpu, x86/pti: Do not enable PTI on AMD processors
That Tom Lendacky memo caught the attention of others too and a few days later an article appeared in "The Register" that exposed Meltdown/Spectre about a week earlier than planned.
When Linus Torvalds saw this memo he realized that Intel was willing to compromise Linux performance on AMD machines so Intel machines would not be the only ones to suffer a performance hit. This apparently triggered his well publicised Intel rant.
I expect Intel did the same thing with Microsoft. Thus, both Linux and MS had to scramble to re-code the changes they had been making to handle Meltdown, likely leading to the Win 10 releases that failed to boot on older AMD processors - still, it's hard to excuse MS for failing to test on at least one older AMD computer.
I've got two older AMD machines with Win 10 (so Spectre 1 is patched). Neither is likely to ever see a BIOS update so there's little choice but to hope that AMD's opinion is correct: Spectre 2 is very difficult to weaponize on AMD. Even the toy versions of Spectre 2 don't work reliably on AMD according to the original reports.
-
-
-
New #56
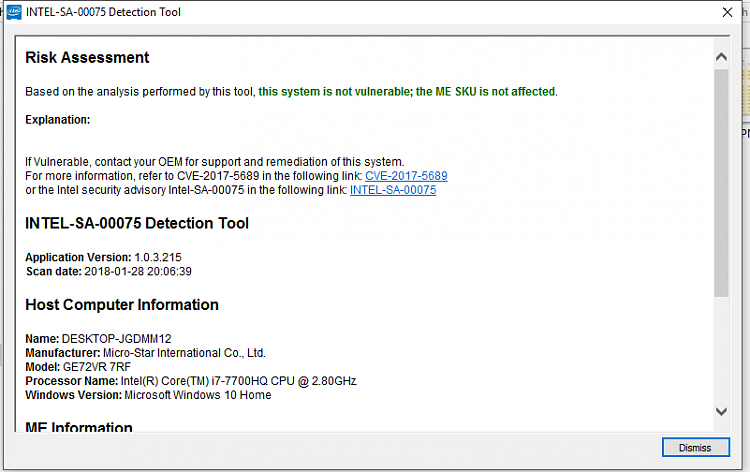
this was mentioned in yesterday's Intel Security Posting too.... about 1/2 way down
Intel Product Security Center
-
New #57
-
-
-
New #59
I got this HP Convertible at the end of December and it has an AMD A9 processor, even though I'm up to date with all necessary Windows updates and since upgraded the BIOS and UEFI firmware from HP for this machine that tool from Steve's site still showed Spectre Protected: NO!
I did read somewhere that even with the necessary patches and upgrades some machines could still be vulnerable though.
Related Discussions



 Quote
Quote