Windows Client Guidance against speculative execution vulnerabilities
-
Hi,
You're most welcome.
Well, what they're saying is that those systems were meant to be stand alones. Sure enough, when you're not connected to a network you're not going to be vulnerable to these kinds of attacks....
Guess they have to draw the line somewhere.

Cheers,

Well, I don't think those "closed systems" are not connected to a network, the reasons evoked have to do more with the micro-architectural characteristics of those old machines precluding the implementation of features capable of mitigating the variant 2 of Spectre (CVE-2017-5715). For reference, you can check the article:
 https://www.helpnetsecurity.com/2018...ocode-updates/
https://www.helpnetsecurity.com/2018...ocode-updates/
-
-
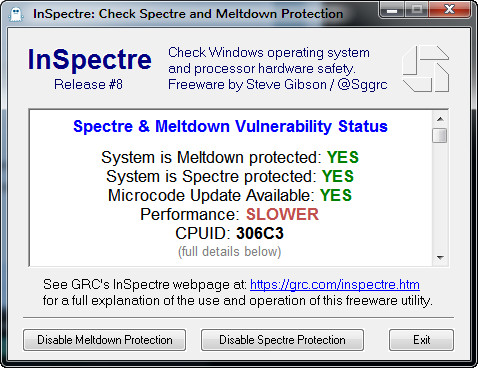
microcode upgrade
Question, where do you download the MC updates from?  shows that the update is available for the Sandy Bridge and Ivy Bridge but now links as to find them. I'm going to assume it's what is in 1803 but according to Steve's InSpectre utility it sounds like an update is out there. Can someone point me in the right direction where you can download these fixes if there is such a place other than upgrade the OS? Thank you.
shows that the update is available for the Sandy Bridge and Ivy Bridge but now links as to find them. I'm going to assume it's what is in 1803 but according to Steve's InSpectre utility it sounds like an update is out there. Can someone point me in the right direction where you can download these fixes if there is such a place other than upgrade the OS? Thank you.
-
Question, where do you download the MC updates from?

shows that the update is available for the Sandy Bridge and Ivy Bridge but now links as to find them. I'm going to assume it's what is in 1803 but according to Steve's InSpectre utility it sounds like an update is out there. Can someone point me in the right direction where you can download these fixes if there is such a place other than upgrade the OS? Thank you.
There was a Microsoft's microcode update patch for Fall Creators's version or build that one could get from the Microsoft Update catalog. It doesn't work for April 2018 Feature version. Maybe they will issue a new one with the next patch Tuesday cumulative update. The only other way to get it is to check your manufacturer's support page in order to have a BIOS/UEFI firmware update.
-
Hi,
Well, I don't think those "closed systems" are not connected to a network, the reasons evoked have to do more with the micro-architectural characteristics of those old machines precluding the implementation of features capable of mitigating the variant 2 of Spectre (CVE-2017-5715). For reference, you can check the article:
 https://www.helpnetsecurity.com/2018...ocode-updates/
https://www.helpnetsecurity.com/2018...ocode-updates/
I did not word that well, my bad. By "Closed System" they mean what exactly ?
The article isn't really clear about that. The way I read it is that most of those machines are either stand alones or on an intranet ??
Or is the CPU's architecture just not capable of speculative code execution ?
Cheers, 
-
-
Or is the CPU's architecture just not capable of speculative code execution ?
Cheers,

That last question of yours is probably what they meant. That's my understanding.
-
Hi,
I doubt any OEM will go back as far as Haswell CPUs but soon enough MS will issue a KB for the April version of W10.
Should you stick to 1709 then you should be fine if you installed KB4090007.
Cheers,

An older laptop I had from 2014 with 4th generation i3 processor which is apparently based on haswell received the "spectre" bios update from HP pretty quickly.
Last edited by tomseys; 03 May 2018 at 01:39.
-
I contacted Gigabyte regarding a MB for a system that showed no update available nor anything in the pipe. They privately linked me to the BIOS/UEFI update. Win 7 system and it is not slow...yet.
Lenovo made updates available for Sandy Bridge laptops ready a couple of months ago. Haven't patched them yet.
-
Which utility do you guys recommend to verify a system is patched? I'm always skeptical of freeware.
-
Which utility do you guys recommend to verify a system is patched? I'm always skeptical of freeware.
I think most people use this: GRC
And you can double/manually check via:
1) Open elevated PowerShell.
2) Temporarily set PowerShell script execution policy
PS> Set-ExecutionPolicy Unrestricted -Scope Process -Force
3) Install the PowerShell module
PS > Install-Module SpeculationControl -Force
Type Y and press Enter if prompted to install and import NuGet.
4) Run the PowerShell module to validate protections are enabled
PS > Get-SpeculationControlSettings
-
-
https://www.helpnetsecurity.com/2018...ocode-updates/




 Quote
Quote