New
#170
they are not the same bug people are confusing them thats why i was confused the other guy wanted the info from my stuff, as i told him that intel me has nothing to do with meltdown and speculation
they are not the same bug people are confusing them thats why i was confused the other guy wanted the info from my stuff, as i told him that intel me has nothing to do with meltdown and speculation
See my earlier post
Windows Client Guidance against speculative execution vulnerabilities - Windows 10 Forums
Shortly:
You're secured for meltdown.
You're partly secured for spectre, the other part comes from firmware updates from your vendor.
Just found this:
Ashampoo Spectre Meltdown CPU Checker 1.0.7 - Neowin
Ashampoo® Spectre Meltdown CPU Checker - Overview
My result:
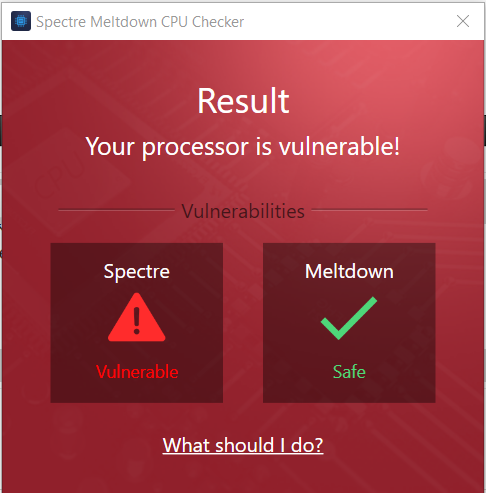
Just found about this on a simulator forum and tried it! Got to admit that makes it simple enough for most to understand.
My Experience Below on ASUS Z170 PRO GAMING with Intel i5 6600K
-= Before =-
-= After looking on ASUS web site =-
-= End Result =-
Code:Infos & Tools https://www.asus.com/us/Motherboards/Z170-PRO-GAMING/HelpDesk_Download/ https://www.intel.com/content/www/us/en/support/articles/000025619/software.html https://downloadcenter.intel.com/download/27150
Here's a small recap with my own additions from Google's Project Zero site:Project Zero
Spectre / Variant 1: bounds check bypass (CVE-2017-5753) Win Update (Program/OS/System No Slowdown)
Mitigation requires analysis and recompilation so that vulnerable binary code is not emitted. Examples of targets which may require patching include the operating system and applications which execute untrusted code.
Spectre / Variant 2: branch target injection (CVE-2017-5715) Bios Update
Mitigating this attack variant requires either installing and enabling a CPU microcode update from the CPU vendor (e.g., Intel's IBRS microcode), or applying a software mitigation (e.g., Google's Retpoline) to the hypervisor, operating system kernel, system programs and libraries, and user applications.
Meltdown / Variant 3: rogue data cache load (CVE-2017-5754) Win Update
Mitigating this attack variant requires patching the operating system. For Linux, the patchset that mitigates Variant 3 is called Kernel Page Table Isolation (KPTI). Other operating systems/providers should implement similar mitigations.
And the Microsoft's own seems to get updated as well with easy explanations.
https://portal.msrc.microsoft.com/en...sory/ADV180002
Best tools for checking your status is the Powershell script and this SpecuCheck program by Alex Ionescu.
Releases · ionescu007/SpecuCheck · GitHub
https://github.com/ionescu007/SpecuC...SpecuCheck.exe
The above 1.05 version shows the correct info on my x64 windows.
Here's what a current fully Spectre and Meltdown patched (windows+bios) system should look like:
@D4ni3l.
Possibly more confusion or just posting in the wrong thread?.
You have only fixed the Intel Management Engine flaw which has got nothing to do with the Meltdown Spectre flaw, different problem, different thread see here from November 2017 Flaws found in Intel Management Engine (ME), TXE and SPS - Windows 10 Forums
Z170 boards have not had a BIOS update for Spectre yet so can not yet be fixed. When it appears it will be a full Bios update with a 2018 date. Z170-Pro requires Bios 7303, until you get that you are not fixed.
Asus have a list of the New Bioses but they have not all been tested and released yet, it will take time. Already linked in one of the threads but See Asus Bios list here ASUS Global
Perhaps a mod can separate the posts referring to the wrong fix out of the relevant threads as it may be confusing people into using the wrong checker and fix thinking they are problem free when they are not.
.
@D4ni3l
Going further, if you visit this page, you get all the info about Intel SA-00086: Intel® Management Engine Critical Firmware Update (Intel-SA-00086)
If you read to the bottom, you'll see this:
Now, if you read the post above by clam, or else go to this link Meltdown and Spectre: What you need to know (CVE-2017-5715, CVE-2017-5753, CVE-2017-5754) you'll see this as the title:Q: What types of access would an attacker need to exploit the identified vulnerabilities?
A: If the equipment manufacturer enables Intel-recommended Flash Descriptor write protections, an attacker needs physical access to platforms firmware flash to exploit vulnerabilities identified in:
CVE-2017-5705
CVE-2017-5706
CVE-2017-5707
CVE-2017-5708
CVE-2017-5709
CVE-2017-5710
CVE-2017-5711
Those are not the same CVE numbers - IOW, SA-00086 has nothing to do with Meltdown or Spectre.Meltdown and Spectre: What you need to know (CVE-2017-5715, CVE-2017-5753, CVE-2017-5754)
Anyone who tells you differently is lying or else does not know what [s]he is talking about at all.
Thanks for that, Mike. Mine failed as well. I see you have one ASUS board with an AMD chip. Same here. I see AMD their article on their site yesterday stating they are working to help to write microcode updates for Ryzen and EPYC processors. I'm concerned whether or not I'll get an updated BIOS to fix the Spectre vulnerability.
Attachment 172220