How to Set PowerShell Script Execution Policy in Windows 10
The PowerShell script execution policies enables you to determine which Windows PowerShell scripts (if any) will be allowed to run on your computer. Windows PowerShell has four different execution policies:
Execution Policy Description AllSigned Only PowerShell scripts signed by a trusted publisher can be run. When you attempt to run a signed script, you'll receive a prompt asking you to confirm that you trust the publisher. Bypass Nothing is blocked and there are no warnings or prompts. Default Sets the default execution policy. Restricted for Windows clients. RemoteSigned for Windows servers. RemoteSigned Downloaded PowerShell scripts must be signed by a trusted publisher before they can be run. Scripts that you run from the local computer don't need to be signed. There are no prompts when you attempt to run a script. Restricted No PowerShell scripts can be run. Windows PowerShell can be used only in interactive mode. This means that you can only run individual commands. You can't run scripts under this policy, regardless of where the scripts came from (local or downloaded) and whether they are signed. Unrestricted Unsigned scripts can run. There is a risk of running malicious scripts. Warns the user before running scripts and configuration files that are downloaded from the internet. Undefined (default) No execution policy has been set. If the execution policy in all scopes is Undefined, the effective execution policy is Restricted, which is the default execution policy.
You can set an execution policy that is effective only in a particular scope.
The Scope values used in this tutorial are Process, CurrentUser, and LocalMachine. LocalMachine is the default when setting an execution policy.
The Scope values are listed in precedence order.
Scope Description Process The execution policy affects only the current session (the current Windows PowerShell process).
The execution policy is stored in the $env:PSExecutionPolicyPreference environment variable, not in the registry, and it is deleted when the session is closed. You cannot change the policy by editing the variable value.CurrentUser The execution policy affects only the current user. It is stored in the HKEY_CURRENT_USER registry subkey. LocalMachine The execution policy affects all users on the current computer. It is stored in the HKEY_LOCAL_MACHINE registry subkey.
The policy that takes precedence is effective in the current session, even if a more restrictive policy was set at a lower level of precedence.
This tutorial will show you different ways on how to set the PowerShell script execution policy for the current user, local machine, or current process in Windows 10.
For a Windows 11 version of this tutorial, see:
Change PowerShell Script Execution Policy in Windows 11
Contents
- Option One: To See Current PowerShell Script Execution Policies
- Option Two: To Set PowerShell Script Execution Policy to "RemoteSigned" for Current User in Settings
- Option Three: To Set PowerShell Script Execution Policy for Current User in PowerShell
- Option Four: To Set PowerShell Script Execution Policy for Current User using a REG file
- Option Five: To Set PowerShell Script Execution Policy for Local Machine in PowerShell
- Option Six: To Set PowerShell Script Execution Policy for Local Machine using a REG file
- Option Seven: To Set PowerShell Script Execution Policy for a Process in PowerShell
1 Open PowerShell.
2 Copy and paste theGet-ExecutionPolicy -Listcommand into PowerShell, and press Enter.
3 You will now see all execution policies. The policies are listed in precedence order. (see screenshot below)
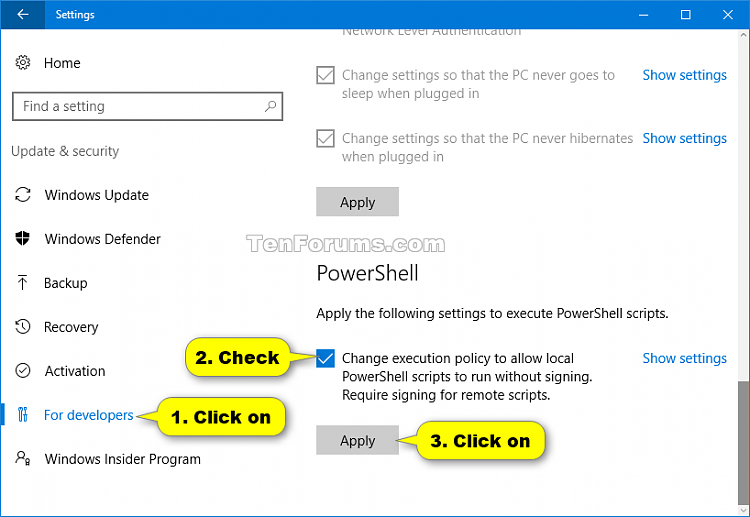
1 Open Settings, and click/tap on the Update & security icon.
2 Click/tap on For developers on the left side, check the Change execution policy to allow local PowerShell scripts to run without signing. Require signing for remote scripts. box under PowerShell on the right side, and click/tap on the Apply button. (see screenshot below)
If this setting is grayed out, then the execution policy for your account is already set to RemoteSigned.
3 You can now close Settings if you like.
1 Open PowerShell.
2 Copy and paste the command below into PowerShell for the execution policy your want to set, and press Enter.
Set-ExecutionPolicy AllSigned -Scope CurrentUser -Force
Set-ExecutionPolicy Bypass -Scope CurrentUser -Force
Set-ExecutionPolicy Default -Scope CurrentUser -Force
Set-ExecutionPolicy RemoteSigned -Scope CurrentUser -Force
Set-ExecutionPolicy Restricted -Scope CurrentUser -Force
Set-ExecutionPolicy Undefined -Scope CurrentUser -Force
Set-ExecutionPolicy Unrestricted -Scope CurrentUser -Force
3 You can now close PowerShell if you like.
The downloadable .reg files below will modify the string value in the registry key below.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell
ExecutionPolicy string value
Restricted
AllSigned
RemoteSigned
Unrestricted
Bypass
Undefined
1 Do step 2 (Restricted), step 3 (AllSigned), step 4 (RemoteSigned), step 5 (Unrestricted), step 6 (Bypass), or step 7 (Undefined) below for what you would like to do.
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
CurrentUser_Restricted_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
CurrentUser_AllSigned_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
CurrentUser_RemoteSigned_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
CurrentUser_Unrestricted_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
CurrentUser_Bypass_PowerShell_ExcutionPolicy.reg
Download
This is the default setting.
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
CurrentUser_Undefined_PowerShell_ExcutionPolicy.reg
Download
8 Save the .reg file to your desktop.
9 Double click/tap on the downloaded .reg file to merge it.
10 When prompted, click/tap on Run, Yes (UAC), Yes, and OK to approve the merge.
11 You can now delete the downloaded .reg file if you like.
You must be signed in as an administrator to be able to do this option.
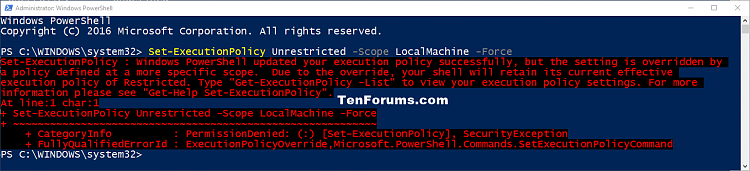
If you get a message in red like below when setting a PowerShell execution policy, then it just means that your (current user) set execution policy will be used instead of this local machine setting. If you like, you can set your (current user) execution policy to Undefined to no longer see this message in red when setting the local machine policy.
1 Open an elevated PowerShell.
2 Copy and paste the command below into the elevated PowerShell for the execution policy your want to set, and press Enter.
Set-ExecutionPolicy AllSigned -Scope LocalMachine -Force
Set-ExecutionPolicy Bypass -Scope LocalMachine -Force
Set-ExecutionPolicy Default -Scope LocalMachine -Force
Set-ExecutionPolicy RemoteSigned -Scope LocalMachine -Force
Set-ExecutionPolicy Restricted -Scope LocalMachine -Force
Set-ExecutionPolicy Undefined -Scope LocalMachine -Force
Set-ExecutionPolicy Unrestricted -Scope LocalMachine -Force
3 You can now close the elevated PowerShell if you like.
You must be signed in as an administrator to be able to do this option.
The downloadable .reg files below will modify the string value in the registry key below.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell
ExecutionPolicy string value
Restricted
AllSigned
RemoteSigned
Unrestricted
Bypass
Undefined
1 Do step 2 (Restricted), step 3 (AllSigned), step 4 (RemoteSigned), step 5 (Unrestricted), step 6 (Bypass), or step 7 (Undefined) below for what you would like to do.
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
LocalMachine_Restricted_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
LocalMachine_AllSigned_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
LocalMachine_RemoteSigned_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
LocalMachine_Unrestricted_PowerShell_ExcutionPolicy.reg
Download
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
LocalMachine_Bypass_PowerShell_ExcutionPolicy.reg
Download
This is the default setting.
A) Click/tap on the Download button below to download the file below, and go to step 8 below.
LocalMachine_Undefined_PowerShell_ExcutionPolicy.reg
Download
8 Save the .reg file to your desktop.
9 Double click/tap on the downloaded .reg file to merge it.
10 When prompted, click/tap on Run, Yes (UAC), Yes, and OK to approve the merge.
11 You can now delete the downloaded .reg file if you like.
The execution policy set in this option affects only the current PowerShell session for the current process until you close the current PowerShell window.
1 While you have a PowerShell or elevated PowerShell open.
2 Copy and paste the command below into PowerShell for the execution policy your want to set, and press Enter.
Set-ExecutionPolicy AllSigned -Scope Process -Force
Set-ExecutionPolicy Bypass -Scope Process -Force
Set-ExecutionPolicy Default -Scope Process -Force
Set-ExecutionPolicy RemoteSigned -Scope Process -Force
Set-ExecutionPolicy Restricted -Scope Process -Force
Set-ExecutionPolicy Undefined -Scope Process -Force
Set-ExecutionPolicy Unrestricted -Scope Process -Force
3 Run any PowerShell scripts you want to run in this PowerShell window (session) using this set execution policy.
4 When finished, you can close PowerShell.
That's it,
Shawn Brink
Related Tutorials
- How to Add Windows PowerShell Script to New Context Menu in Windows 10
- How to Add 'Run as administrator' to PS1 File Context Menu in Windows 10
- How to run PowerShell scripts from a Shortcut
Change PowerShell Script Execution Policy in Windows 10
-
New #1
I ran Option 2 which gave the settings below. How do I reset the permissions back to the default Undefined?
Attachment 170968
-
-
New #3
-
New #4
Very Well Done!
Simply want to complement you on the tutorial; it's very well done.
Thanks!
-
New #5
Shawn,
The MSDocs reference page still shows that the argument Bypass is valid but you do not include that. Is there a reason?
I have recently [probably since the Ver 1903 update] had a few problems with a couple of batch files and am now starting to investigate them. So if you know something I don't I'd want to amend my current [batch file] powershell.exe -ExecutionPolicy ByPass -File ... references as I go along.Code:-ExecutionPolicy Specifies the execution policy. If there are no Group Policies and each scope's execution policy is set to Undefined, then Restricted becomes the effective policy for all users. The acceptable execution policy values are as follows:
- AllSigned. Requires that all scripts and configuration files are signed by a trusted publisher, including scripts written on the local computer.
- Bypass. Nothing is blocked and there are no warnings or prompts.
- Default. Sets the default execution policy. Restricted for Windows clients or RemoteSigned for Windows servers.
- RemoteSigned. Requires that all scripts and configuration files downloaded from the Internet are signed by a trusted publisher. The default execution policy for Windows server computers.
- Restricted. Doesn't load configuration files or run scripts. The default execution policy Windows client computers.
- Undefined. No execution policy is set for the scope. Removes an assigned execution policy from a scope that is not set by a Group Policy. If the execution policy in all scopes is Undefined, the effective execution policy is Restricted.
- Unrestricted. Loads all configuration files and runs all scripts. If you run an unsigned script that was downloaded from the Internet, you are prompted for permission before it runs.
All the best,
Denis
-
-
New #7
Thanks.
I can discount that as a cause of my current problem - some PowerShell scripts initiated by batch files no longer do what they once did.
I have been using a couple of PowerShell functions I found on the internet a year or more ago to alter the NightLight in response to switching between my powerplans but they no longer have any effect at all. Just by way of example, if I play videos back over HDMI I want to prevent the NightLight kicking in & altering the display so I switch to my "BalancedOn" powerplan using a batch file that included invoking these PS functions [as well as running a few other odd jobs such as volume control].
Denis
-
New #8
Disabling PowerShell script execution / Restricting PowerShell to Constrained Language mode
Source: Hard_ConfiguratorCode:Set-ExecutionPolicy bypass - noprofile reg add "HKLM\Software\Policies\Microsoft\Windows\PowerShell" /v "EnableScripts" /t REG_DWORD /d "0" /f reg add "HKLM\System\CurrentControlSet\Control\Session Manager\Environment" /v "__PSLockDownPolicy" /t REG_SZ /d "4" /f
-
-
New #9
hi
under w10 pro 64bit
the default is like windows 11
but under w10 i can execute a power shell script with the right click mouse run with powershell ,under w11 it doesn't work
i know it's a w10 forum but related to w11 since i have posted even in the w11 forum
Code:Get-ExecutionPolicy -List Scope ExecutionPolicy ----- --------------- MachinePolicy Undefined UserPolicy Undefined Process Undefined CurrentUser Undefined LocalMachine Undefined

Change PowerShell Script Execution Policy in Windows 10
How to Set PowerShell Script Execution Policy in Windows 10Published by Shawn BrinkCategory: General Tips
23 Feb 2023
Tutorial Categories
Related Discussions



 Quote
Quote
