How to Disable Early Launch Anti-Malware Protection in Windows 8 and Windows 10
Information
As antimalware (AM) software has become better and better at detecting runtime malware, attackers are also becoming better at creating rootkits that can hide from detection. Detecting malware that starts early in the boot cycle is a challenge that most AM vendors address diligently. Typically, they create system hacks that are not supported by the host operating system and can actually result in placing the computer in an unstable state. Up to this point, Windows has not provided a good way for AM to detect and resolve these early boot threats.
Windows 8 and Windows 10 include a feature called Secure Boot, which protects the Windows boot configuration and components, and loads an Early Launch Anti-malware (ELAM) driver. This driver starts before other boot-start drivers and enables the evaluation of those drivers and helps the Windows kernel decide whether they should be initialized.
For more details about Early Launch Anti-malware, see:
If a driver is classified as malware by Early Launch Anti-Malware because it is malicious or because of a false positive, the driver may not be allowed to load. If this is a necessary driver for Windows to start properly, then Windows may be unable to boot up properly. To help prevent this, you can temporarily disable early-launch anti-malware protection during a boot so that you can resolve your issues by either updating your virus detections or removing the problematic malware driver. The next time you restart your computer, early-launch anti-malware protection will automatically be enabled again.
This tutorial will show you how to temporarily disable Early Launch Anti-Malware protection as needed in Windows 8 and Windows 10.
You must be signed in as an administrator to be able to disable Early Launch Anti-Malware protection.
Here's How:
1. Boot to advanced startup options on your Windows 8 or Windows 10 PC.
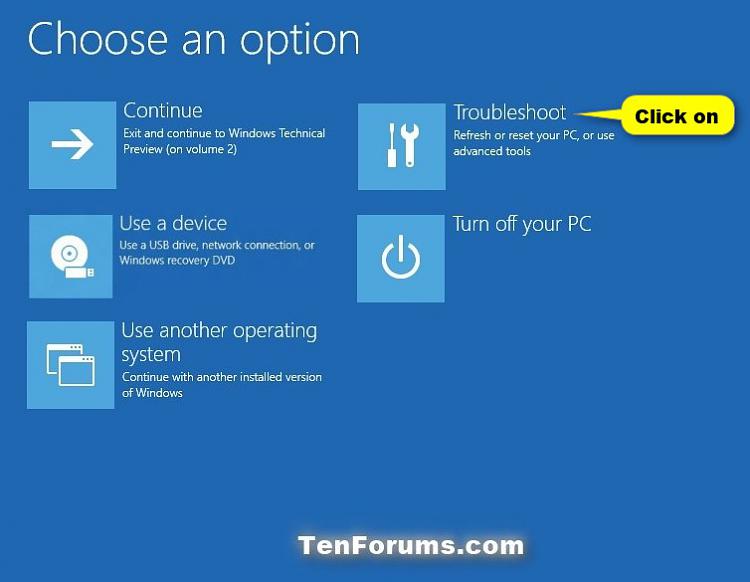
2. Click/tap on Troubleshoot. (see screenshot below)
3. Click/tap on Startup Settings. (see screenshot below)
4. Click/tap on Restart. (see screenshot below)
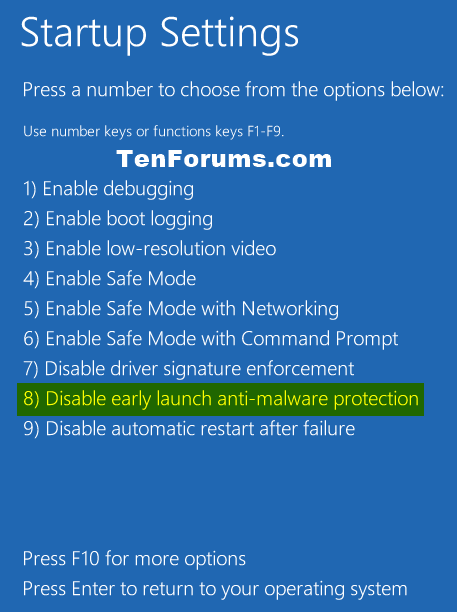
5. Press the 8 or F8 key on your keyboard to Disable early-launch anti-malware protection. (see screenshot below)
6. Windows will now start with early-launch anti-malware protection disabled. The next time you restart the computer, early-launch anti-malware protection will automatically be enabled again.
That's it,
Shawn
Related Tutorials
- How to Configure Early Launch AntiMalware Boot-Start Driver Initialization Policy in Windows 8 and 10
- How to Perform a Clean Boot in Windows 10 to Troubleshoot Software Conflicts
Disable Early Launch Anti-Malware in Windows 8 and Windows 10

Disable Early Launch Anti-Malware in Windows 8 and Windows 10
How to Disable Early Launch Anti-Malware Protection in Windows 8 and Windows 10Published by Shawn BrinkCategory: Security System
14 Mar 2017
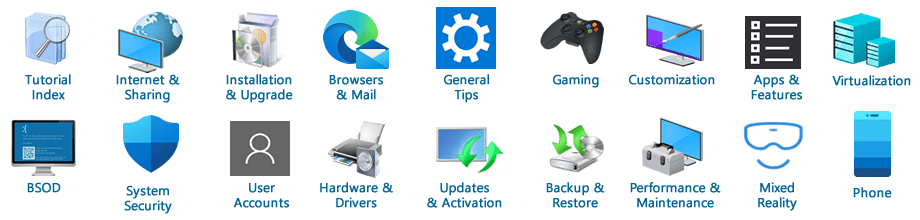
Tutorial Categories
Related Discussions