How to Check if Windows PC has a Trusted Platform Module (TPM) Chip
Trusted Platform Module (TPM) technology is designed to provide hardware-based, security-related functions. A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations. The chip includes multiple physical security mechanisms to make it tamper resistant, and malicious software is unable to tamper with the security functions of the TPM. Some of the key advantages of using TPM technology are that you can:
- Generate, store, and limit the use of cryptographic keys.
- Use TPM technology for platform device authentication by using the TPMs unique RSA key, which is burned into itself.
- Help ensure platform integrity by taking and storing security measurements.
"Almost every CPU in the last 5-7 years has a TPM. For Intel its called the "Intel PTT" which you set to enabled. For AMD it would be "AMD PSP fTPM". TPMs have been required for OEM certification since at least 2015 and was announced in 2013," said David Weston, Director of Enterprise and OS Security at Microsoft.
The most common TPM functions are used for system integrity measurements and for key creation and use. During the boot process of a system, the boot code that is loaded (including firmware and the operating system components) can be measured and recorded in the TPM. The integrity measurements can be used as evidence for how a system started and to make sure that a TPM-based key was used only when the correct software was used to boot the system.
TPM-based keys can be configured in a variety of ways. One option is to make a TPM-based key unavailable outside the TPM. This is good to mitigate phishing attacks because it prevents the key from being copied and used without the TPM. TPM-based keys can also be configured to require an authorization value to use them. If too many incorrect authorization guesses occur, the TPM will activate its dictionary attack logic and prevent further authorization value guesses.
Different versions of the TPM are defined in specifications by the Trusted Computing Group (TCG).
Windows can automatically provision and manage the TPM. Group Policy settings can be configured to control whether the TPM owner authorization value is backed up in Active Directory. Because the TPM state persists across operating system installations, TPM information is stored in a location in Active Directory that is separate from computer objects. Depending on an enterprises security goals, Group Policy can be configured to allow or prevent local administrators from resetting the TPMs dictionary attack logic. Standard users can use the TPM, but Group Policy controls limit how many authorization failures standard users can attempt so that one user is unable to prevent other users or the administrator from using the TPM. TPM technology can also be used as a virtual smart card and for secure certificate storage. With BitLocker Network Unlock, domain-joined computers are not prompted for a BitLocker PIN.
For more details about TPM, see:
- Trusted Platform Module Technology Overview | Microsoft Docs
- TPM recommendations (Windows 10) | Microsoft Docs
- Trusted Platform Module (Windows 10) | Microsoft Docs
- Trusted Plaform Module (TPM) 2.0 | Microsoft Docs
- BitLocker TPM Requirement FAQs | Microsoft Docs
- Enable TPM 2.0 on your PC | Microsoft Support
This tutorial will show you how to check if your Windows PC has a Trusted Platform Module (TPM) security hardware chip, and to see your TPM details and version if available.
Contents
- Option One: To See if PC has a TPM and TPM Details in Device Manager
- Option Two: To See if PC has a TPM and TPM Details in TPM Management snap-in console
- Option Three: To See if PC has a TPM and TPM Details in BIOS or UEFI Firmware Settings
- Option Four: To See if PC has a TPM and TPM Details in Windows Security
- Option Five: To See if PC has a TPM and TPM Details in Command Prompt
- Option Six: To See if PC has a TPM and TPM Details in PowerShell
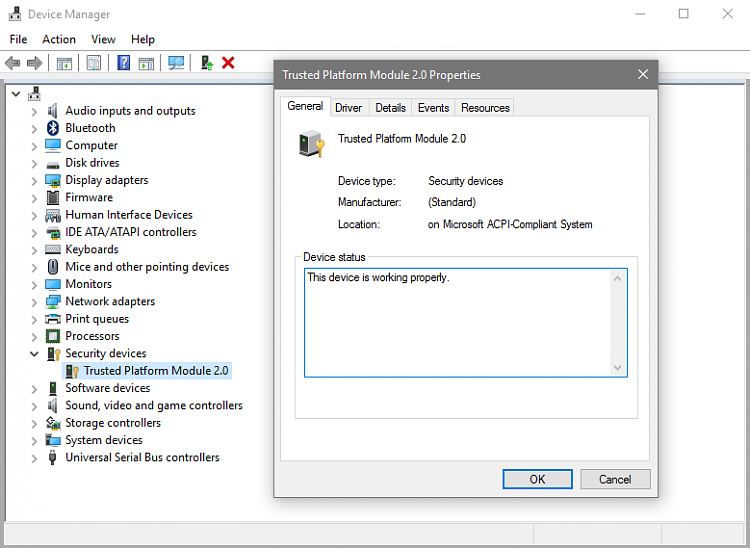
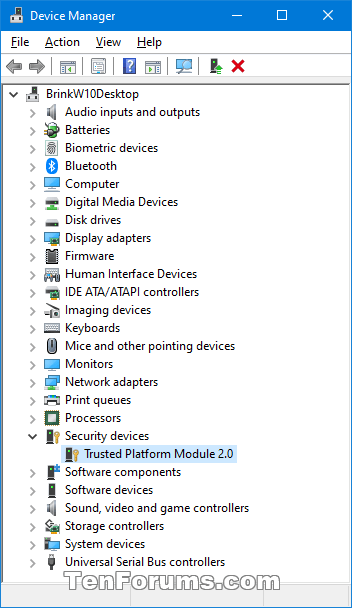
1 Open Device Manager.
2 Look to see if you have Security devices listed. If you do, then expand it open to see if you have a Trusted Platform Module device listed with a version number (ex: 2.0).
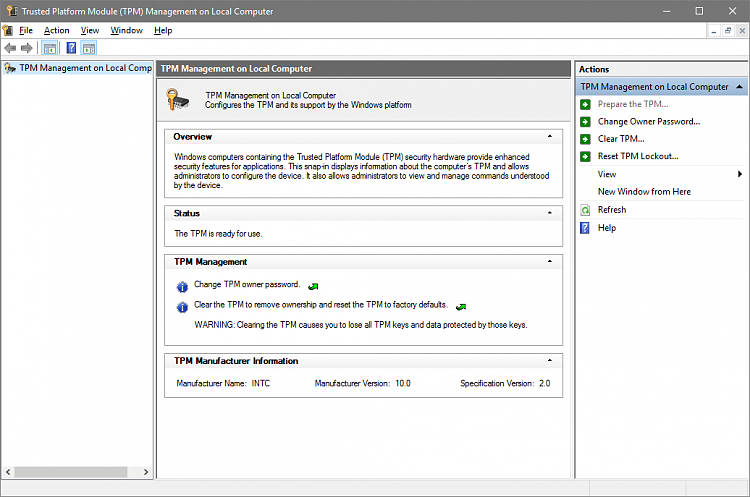
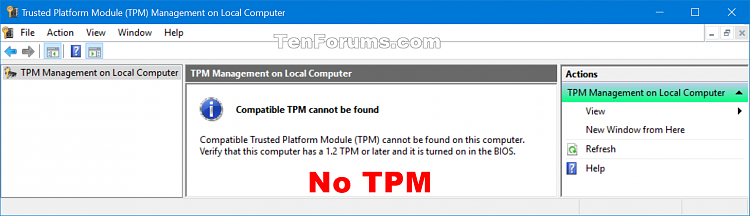
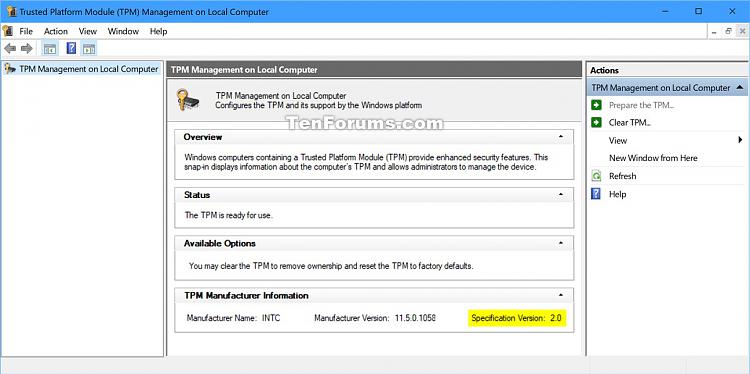
1 Press the Win + R keys to open Run, type tpm.msc into Run, and click/tap on OK to open the TPM Management snap-in.
2 Look to see if the TPM Management console shows your PC having a TPM available or not.
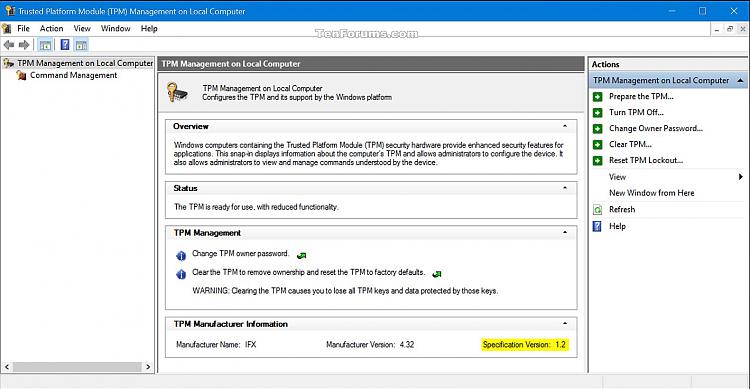
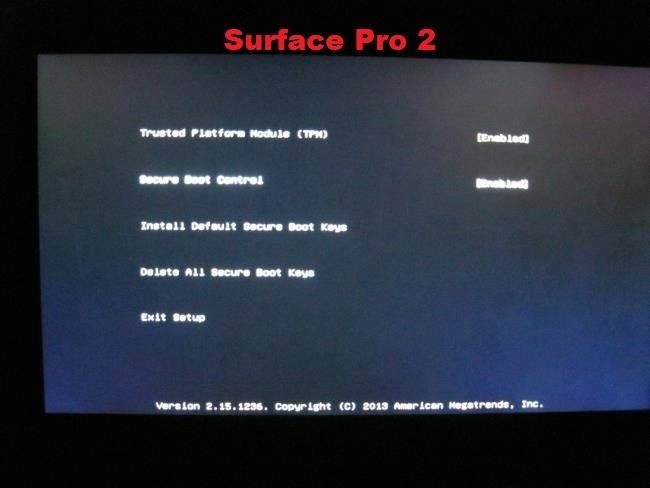
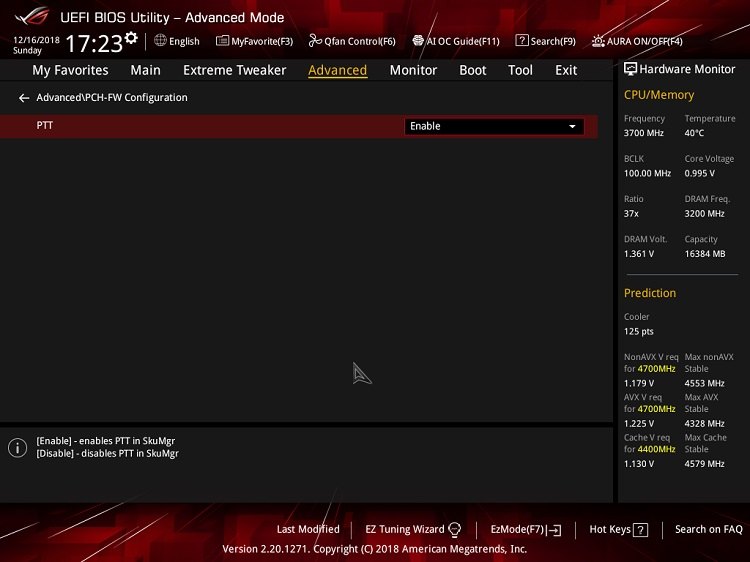
1 Boot the computer to BIOS or UEFI firmware settings.
2 Look to see if you may have a Trusted Platform Module (TPM) or PTT type setting to enable or disable.

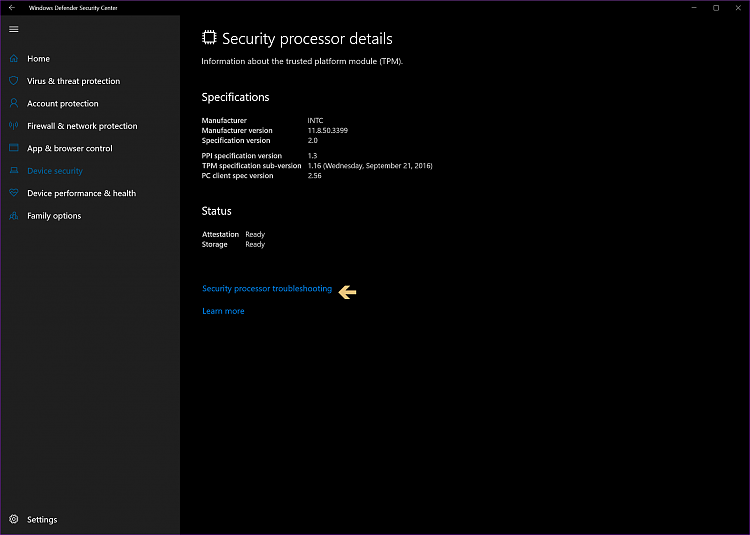
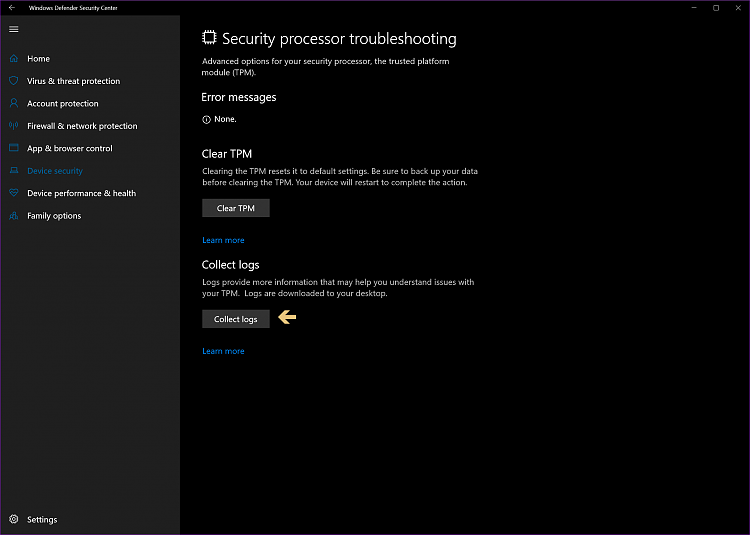
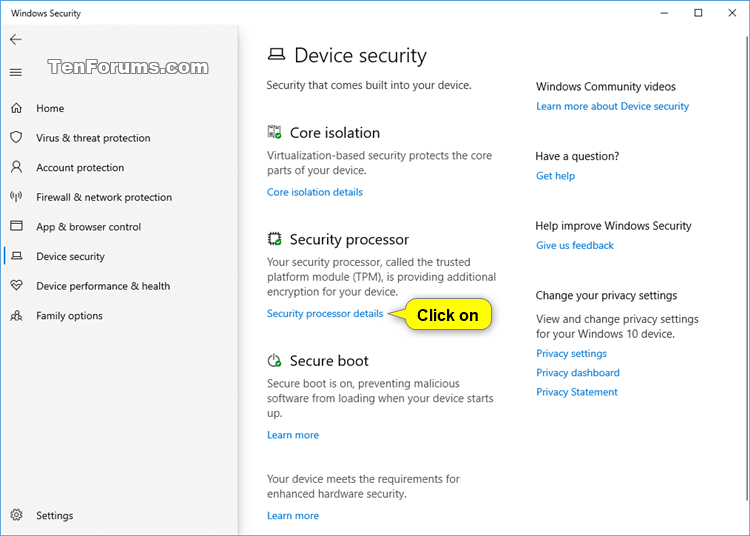
1 Open the Windows Security, and click/tap on the Device Security icon. (see screenshot below)
2 Click/tap on the Security processor details link under Security processor. (see screenshot below)
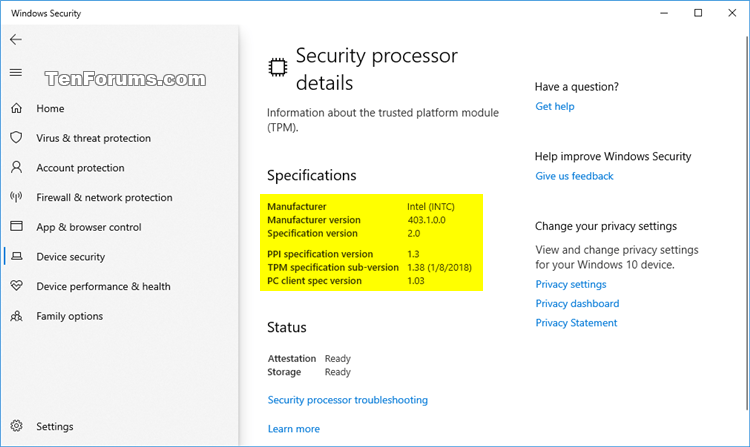
3 If you have a TPM, you will now see general information about it. (see screenshot below)
4. When finished, you can close Windows Security.
To see more usage details about the tpmtool command, see: tpmtool | Microsoft Docs
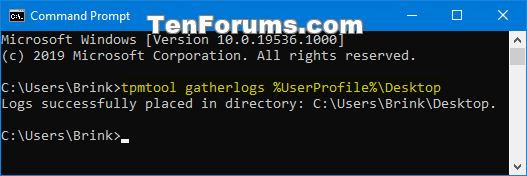
1 Open a command prompt.
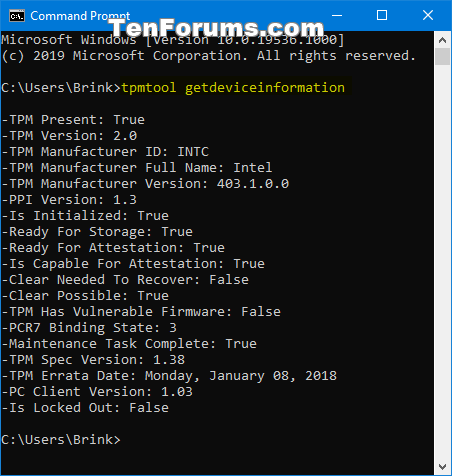
2 Copy and paste the command below you want to use into the command prompt, and press Enter. (see screenshots below)
(To output TPM general details in command prompt)
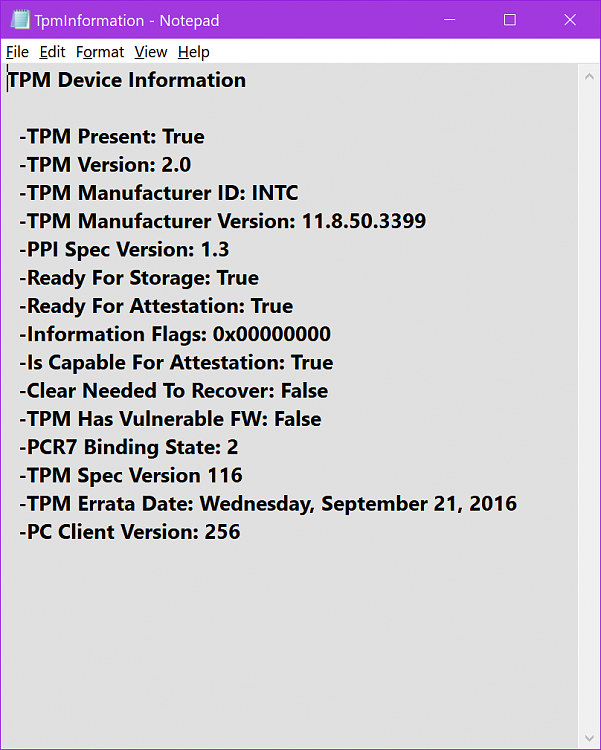
tpmtool getdeviceinformation
OR
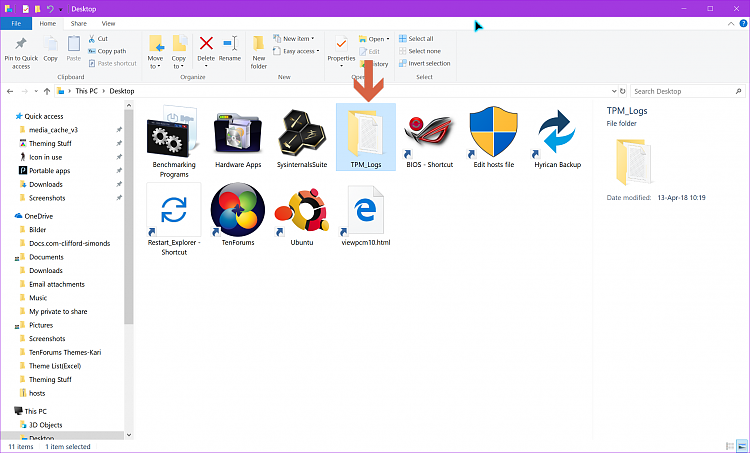
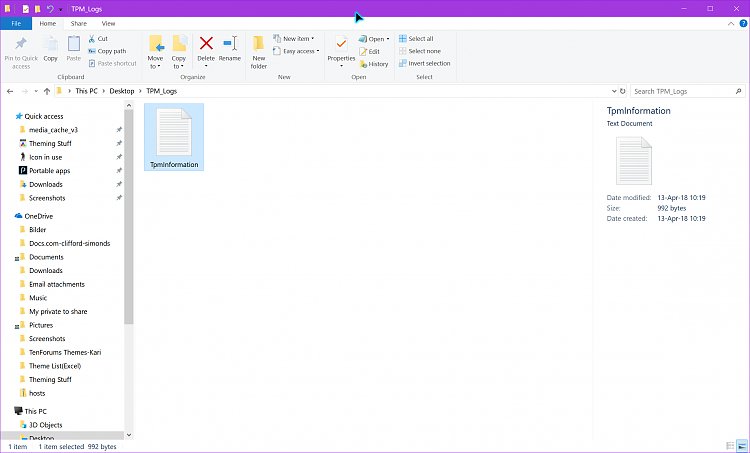
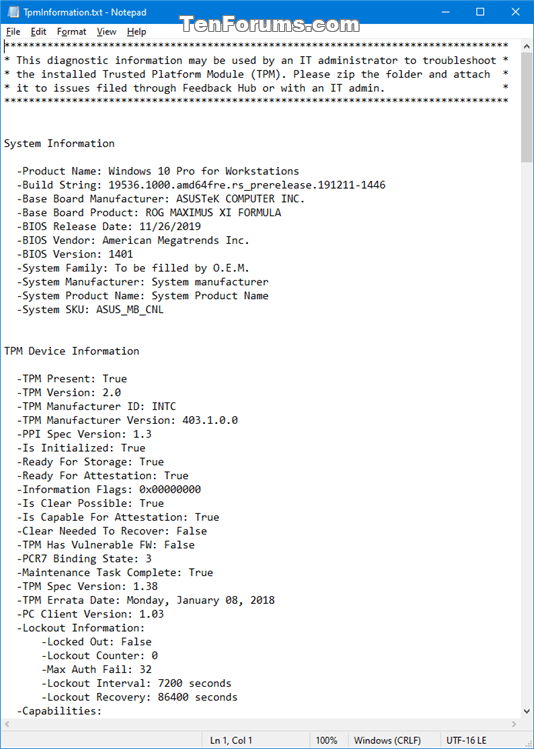
(To output TPM more details to TpmInformation.txt file on desktop)
tpmtool gatherlogs %UserProfile%\Desktop
Collects TPM logs and places them on your desktop. The possible files generated are:
- TpmEvents.evtx
- TpmInformation.txt
- SRTMBoot.dat
- SRTMResume.dat
- DRTMBoot.dat
- DRTMResume.dat
You must be signed in as an administrator to do this option.
To see more usage details about the Get-Tpm command, see: Get-Tpm | Microsoft Docs
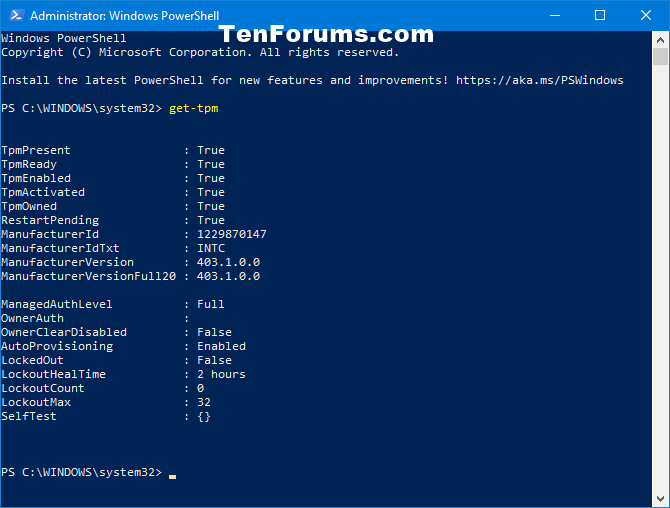
1 Open an elevated PowerShell.
2 Copy and paste the command below you want to use into the elevated PowerShell, and press Enter to see if True or False is reported for a TPM. (see screenshots below)
(Detailed)
get-tpm
OR
(Non-detailed)
get-tpm | select -ExpandProperty tpmpresent
That's it,
Shawn Brink
Related Tutorials
- Check TPM version in Windows 10 and Windows 11
- Install or Uninstall TPM Diagnostics Tool in Windows 11
- Bypass Windows 11 System Requirements
Verify Trusted Platform Module (TPM) Chip on Windows PC
-
New #1
Something I came across not long ago, is Firmware-based Trusted Platform Modules (fTPM). Whereas before in order to take advantage of a TPM you needed to have a physical TPM chip soldered to the motherboard, that seems to have changed at some point. You can now have either a Discrete TPM (Physical chip) or Firmware-based TPM.
As per THIS article, fTPM is acknowledged by the Trusted Computing Group (TCG) as a perfectly valid form of TPM and seems to perform much the same functions as a physical TPM. For Intel, their fTPM is called Intel Platform Trust Technology (PTT). I don't know what chips/motherboards/BIOS support PTT, however due to it being Firmware based (as the name suggests) and not requiring a separate physical chip, it means for some devices it's possible to retrospectively add a TPM to devices that didn't have one before.
Looking through the Intel NUC list, it's not just 6th gen Skylake NUC's that it's supported on, but also 5th gen Broadwell NUC's and 4th gen Haswell NUC's too. So if you have a NUC and you have the latest BIOS, then the chances are you have a TPM 2.0 module even if you didn't think you did. You just need to enable 'Intel Platform Trust Technology' in BIOS. As previously mentioned, I don't know what other manufacturers support/will support fTPM too.
The Intel Platform Trust Technology (PTT) setting in Intel VisualBIOS:
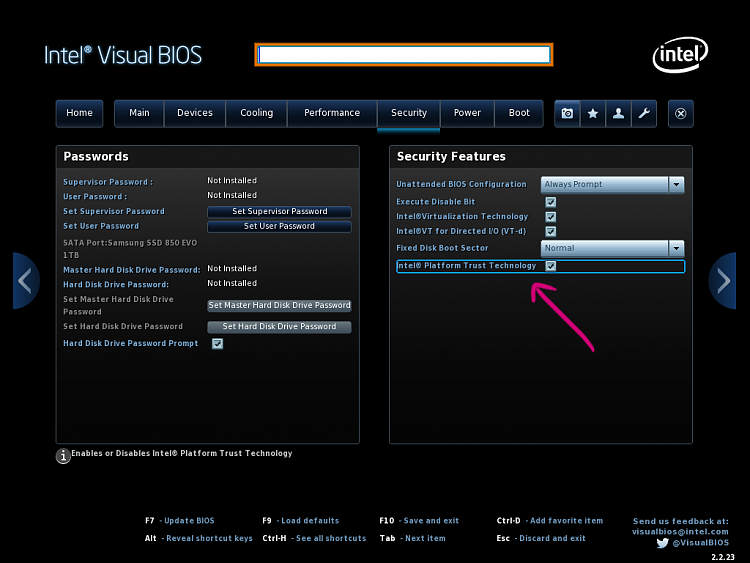
With Intel PTT on in BIOS, Device Manager and tpm.msc show a TPM 2.0 module installed.
-
New #2
@ARC1020, v2.0 is new and is firmware based They want people to have the ability to purchase firmware that has fTPM 2.0 so one doesn't have to go out and buy a motherboard with a TPM header, swap all the internals of their PC, install drivers, etc. Having fTPM is superior in every way to TPM 1.2 using a daughter card.
I will simply not use daughter card TPM (1.2). I will only use fTPM 2.0. That said, Black Hat was able to crack TPM years ago, and people with a good know-how about semiconductors can "unlock" them, so it's never wise to just rely on even the fTPM.
For my office desktop, I use 2 SED (self-encrypting drives) that encrypts any and all data on-the-fly with FIPS 140-2 certification utilizing a Secure Erase feature that destroys the drive if tampered with when it's physically put in a locked state.
For those who do not have a TPM mobo, it's very easy to self-assign a certificate with a Yubikey so Windows recognizes it as a PIV (smart card), trust the certificate and have your own portable TPM. I issue myself a certificate from my server's CA and use my Yubikey in unison with my SED with TPM 2.0 chipset integration (more on this below in the "**EDIT**." For my work laptop, I also use a SED + TPM + Yubikey. Per most of what I'm contracted out to do, I'm always given smart cards for encryption/access, but I can't stand the size of smart cards and the reader you use with them, so I have them load the certificates on my Yubikey 4, which I then transfer to my backup Yubikey.
**EDIT**
Also, daughter card TPMs are, in my opinion, wastes of money if you are truly trying to keep things safe on your PC. Sure, cryptography sticks even if someone removes the daughter card from the TPM header on the mobo, but they run on Low Bus Count (LBC), making them EXTREMELY easy to manipulate. If you are going for TPM, you want chipset integration. Intel's does this with their vPro technology, which utilizes the TPM to run as an application within the Management Engine on the new architecture's Platform Control Hub.Last edited by DrEmpiricism; 06 Oct 2016 at 12:31.
-
New #3
TPM 2.0 isn't really new (2014) and you are aware I suppose that you can use bitlocker with hardware based encryption.
Are you suggesting you could pull out the TPM daughter card replace it and then somehow unlock the drive? Or are you saying TPM isn't secure at all?
Surely if it was an issue someone would have mentioned it. Should I give up on encryption then as it is all so easily bypassed?
Or is using bitlocker with hardware encryption still the way forward?
-
New #4
2.0 is new in respect to how it works, which is eons ahead of what 1.2 did/does. Even now, the majority of motherboards simply use a TPM header and require you to purchase a daughter board, which, yes, can come in either 1.2 or 2.0 versions; however, the versions are irrelevant when it comes to the fact they all run in LBC, greatly increasing the ability of semiconductor and pin manipulation and duplication. fTPM 2.0 relies on a backup method of the cryptography of its already significantly better firmware engaged TPM by having it act within the Management Engine on the Platform Control Hub. That in itself is substantial since there are constant and erratic fluctuations in the resistivity of the conductor material. This can be due to factors built in, owner/user changes, etc. Even in itself, with a daughter card TPM 1.2, or soldered TPM module, semiconductor manipulation is extremely difficult, and why machine code/electronic code algorithms are the most difficult types to interpret and code. It's also not something you can just take up in a few classes, either. This kind of manipulation needs to be oriented towards and takes years to learn, and even then, you have firmware updates to accommodate.
I never suggested you could pull out the TPM daughter card in any way and thus access the drive as if TPM never existed. The cryptography has already been processed and the encryption has already been done. Just like if you use Bitlocker on a USB drive, simply unplugging it from the host system and plugging it in elsewhere does not remove the encryption. Encryption like that would be worse than open-source software encryption.
You should never give up on encryption, but always remember that encryption is only as good as the methods used to encrypt. To simply have encryption on something is all well and good for moderate sensitive material; however, for critical information, processes, databases, etc. encryption is simply a layer of solid data security. It is not solid data security in itself.
Bitlocker is mediocre. It works, yes, but it's just your basic encryption, even if you adjust the cipher settings in User/Group Policies. As an example, formatting a Bitlocked drive can be done without any backup verification. Formatting a Bitlocked drive most ways is like not using Bitlocker period because that data/partition will be easily rendered readable by many, many types of software (and a lot of freeware). An average person with the right software from the internet could format a Bitlocked drive to clear the encryption, then use a recovery tool to re-initialize that partition in an unlocked state or simply batch extract all files on the drive. Bitlocker is simply encryption designed to make you feel warm and cozy at night. A much better encryption type, that's free, is VeraCrypt. Its algorithms are robust, it uses containers (including hidden containers). Using something like VeraCrypt to create an encrypted container on a drive that has been encrypted with Bitlocker increases the safety of your material astronomically.
As stated before, though, hardware encryption will ALWAYS supersede software encryption. Always. Using Bitlocker in conjunction with hardware-based authentication greatly increases Bitlocker's viability and security. Hardware encryption can be pricey, but you have to gauge the cost with how confident you feel about the security of your data.
Conclusively, for the average user, Bitlocker does what it's suppose to, is fully integrated into the OS, and works (all things considering). For any user out of that aforementioned range of "average," I would investigate additional methods of encryption (like I said with using a high-cipher encrypted container with something like Veracrypt in combination with Bitlocker). If you're dealing with such things as HIPPA, medical dictations, lists of passphrases you use to access an outside secure environment, etc., you need to start looking at pure hardware encryption and not Bitlocker with TPM or Smart Card, or Heaven forbid, just Bitlocker alone.
-
New #5
Let me be clear here: I do not want people to think Bitlocker is worthless. Bitlocker works well for what it's designed to do: Safekeep what sound-minded people would keep on a personal computer. Its creation was never intended to be a concrete safety "vault."
Using hardware + Bitlocker is the route one should go when using Bitlocker outside the range of just storing their porn folder or "warez." Hardware cryptography + encryption is a great combination. For those who have a motherboard lacking a TPM header, a Yubikey 4 can be purchased for $40 and work better because it's removable and not just a perepherial added to the motherboard.
Even using Bitlocker in conjunction with 7zip's AES-512 to protect a collection of files works well, and again, it's free.
I personally use a VeraCrypt container on a Bitlocked drive that is Yubikey unlocked for safe keeping moderate personal records and documents. It's an excellent combination. VeraCrypt alone surpasses 99% of paid encryption software. Features like TRULY hidden containers work exceptionally well: You will never find them, a format removes the encrypted container holding encrypted information, so the data is unrecoverable (by the great majority of software the public has access to). Even when I have done a low-level format of a Bitlocked partition with an encrypted VeraCrypt container, then used the means I have to restore the encrypted files, 99% of them were corrupt upon restoration. Using Bitlocker alone, though? I can restore a partition you format over 200+ times. write zeros to, 2-3 pass "wipers," etc. with very little data corruption.
If you want something hardware exclusive that's cheaper, take at hardware encrypted flash drives. You can find AES-256+ units, or FIPS 140-2 validated USB 3.0 flash drives that are not that expensive. From there you get all the way up into what I use for my home office (due to the work I do).
Sidenote: Always use a nice, long PIN to secure anything software locked. They're always more secure, no matter how obnoxious your password was going to be.
-
New #6
-
-
New #8
-
-

Verify Trusted Platform Module (TPM) Chip on Windows PC
How to Check if Windows PC has a Trusted Platform Module (TPM) ChipPublished by Shawn BrinkCategory: Hardware & Drivers
12 Oct 2023
Tutorial Categories
Related Discussions




 Quote
Quote