New
#1
Windows Credentials
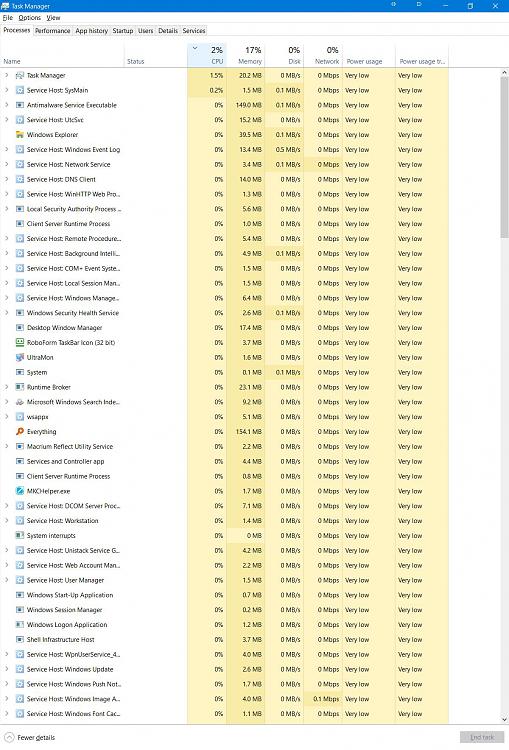
I am at the lookout for why my folders and files takes about 5-10 seconds to open, and I discovered a slew of security events at the same time (same second; in the Event Viewer) and I figured that while it may have nothing to do with my slowness, I might as well ask to see.
In ...
Administrative Tools > Event Viewer > Windows Logs > Security
... I have this:
Credential Manager credentials were read (among other items:
Account name: DESKTOP-xxxxxx#$ (letters: x; digits: #; $ as itself)
When I check in the Credentials Manager, this account name does not occur there (others do). Is this as it should be, or do I have older credentials that slow things down as they are searched for?
Should I delete all credentials? Would the correct ones be recreated?
Grateful for some info on this for me rather obscure issue.
Oh, Windows 10, 64-bit, v 20H2.
Hans L


 Quote
Quote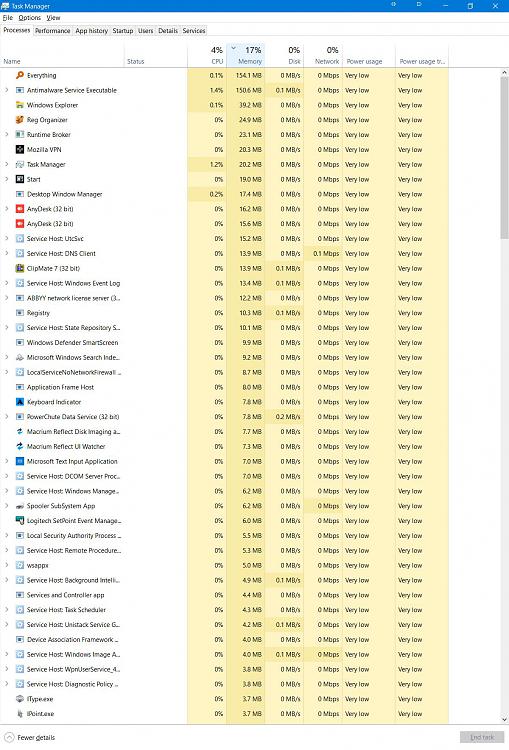
 Thanks, that sounds good... that things were fine in Safe Mode immediately suggests some effect of an installed program, and it seems you were lucky enough to pick the right one.
Thanks, that sounds good... that things were fine in Safe Mode immediately suggests some effect of an installed program, and it seems you were lucky enough to pick the right one.
 )
)