New
#1
W11 BSOD - various events, how to debug?
Recently my W11 (23H2) (-Pro) machine had a few times with BSOD crashes with no apparent reason, saying: Unexpected Kernel mode trap,
And System Thread Exception not handled, and then on reboot did not start properly.
In addition, it is very slow sometimes sluggish program starts, gaps in response, etc.
Also a few: "Video Scheduler internal error" crashes.
Debugging minidumps only one showed a possible (user program) cause, and rest are system events & exceptions.
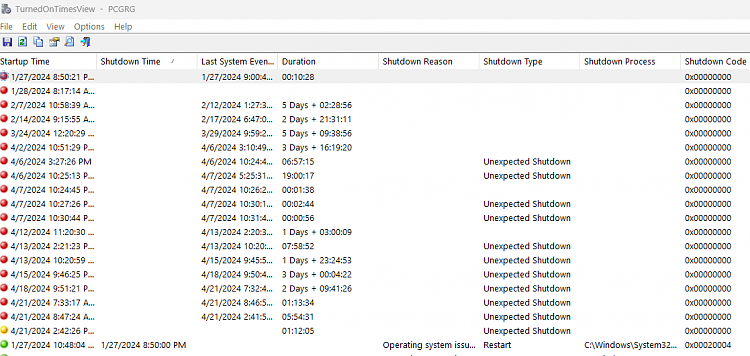
But now I also started getting unexpected shutdowns, with an automatic restart that fails.
Thus I come back to my maching the next day, and it shows a BSOD with the message
your machine did not start properly
But I can choose try again and it works fine.
I seem to get these every few days.
Again looking at minidump(s) and events, I dont see any apparent cause (Event code = 0000 .).
I have turned on Windows Driver Verifier.
Both Dell and MSoft updates all installed.
Minidumps (& WinDbg) seem to generally just show it is in the kernel, although one recent one pointed to firefox.
Etc.Code:BLACKBOXWINLOGON: 1 CUSTOMER_CRASH_COUNT: 1 PROCESS_NAME: SearchProtocolHost.exe --------- BLACKBOXWINLOGON: 1 CUSTOMER_CRASH_COUNT: 1 PROCESS_NAME: firefox.exe --------- BLACKBOXWINLOGON: 1 CUSTOMER_CRASH_COUNT: 1 PROCESS_NAME: System MODULE_NAME: stornvme IMAGE_NAME: stornvme.sys ------- BLACKBOXWINLOGON: 1 CUSTOMER_CRASH_COUNT: 1 PROCESS_NAME: System IMAGE_NAME: ntkrnlmp.exe --------- SYMBOL_NAME: nt!KiDoubleFaultAbort+340 MODULE_NAME: nt IMAGE_NAME: ntkrnlmp.exe ---------
And I just got these two:
VIDEO_SCHEDULER_INTERNAL_ERROR (119)
Driver IRQL not less or equal
Kfecollx64.exe
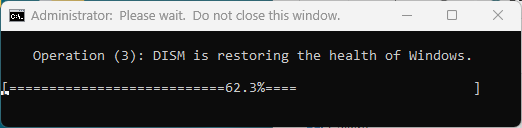
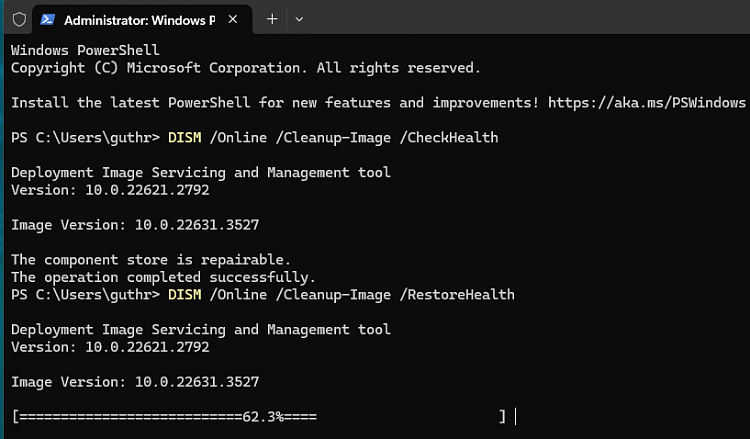
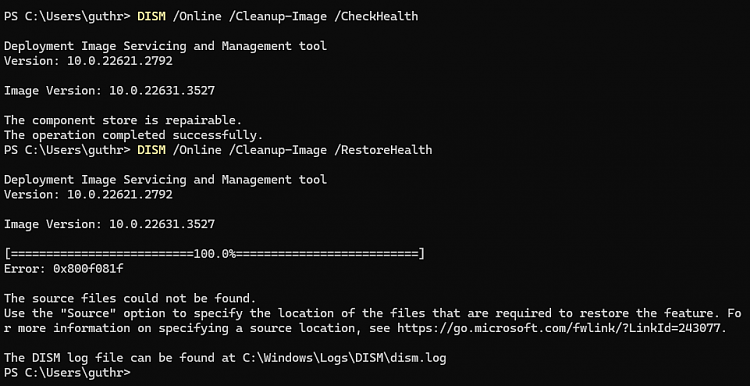
I ran sfc, it reported some files fixed (I did not see which ones).
What would be a good next step in debugging this?
Log files here: https://www.dropbox.com/t/dNn62kqMkEA0jbEP
I ran Microsoft Malware removal (Microsoft Safety scanner), it ran for 80+ hours (!) and checked 78m items, found nothing.
I run Malwarebytes scans daily.
Code:Sample Minidump: IRQL_NOT_LESS_OR_EQUAL (a) An attempt was made to access a pageable (or completely invalid) address at an interrupt request level (IRQL) that is too high. This is usually caused by drivers using improper addresses. If a kernel debugger is available get the stack backtrace. Arguments: Arg1: ffff8089a2e40ff8, memory referenced Arg2: 0000000000000002, IRQL Arg3: 0000000000000001, bitfield : bit 0 : value 0 = read operation, 1 = write operation bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status) Arg4: fffff80265872227, address which referenced memory Debugging Details: ------------------ KEY_VALUES_STRING: 1 Key : Analysis.CPU.mSec Value: 1828 Key : Analysis.Elapsed.mSec Value: 8603 Key : Analysis.IO.Other.Mb Value: 0 Key : Analysis.IO.Read.Mb Value: 0 Key : Analysis.IO.Write.Mb Value: 1 Key : Analysis.Init.CPU.mSec Value: 375 Key : Analysis.Init.Elapsed.mSec Value: 4797 Key : Analysis.Memory.CommitPeak.Mb Value: 94 Key : Bugcheck.Code.LegacyAPI Value: 0xa Key : Bugcheck.Code.TargetModel Value: 0xa Key : Failure.Bucket Value: AV_VRF_KfeCo11X64!unknown_function Key : Failure.Hash Value: {a8dd5be4-b28a-4e52-c33f-ed40455b8b0f} Key : Hypervisor.Enlightenments.ValueHex Value: 1417df84 Key : Hypervisor.Flags.AnyHypervisorPresent Value: 1 Key : Hypervisor.Flags.ApicEnlightened Value: 0 Key : Hypervisor.Flags.ApicVirtualizationAvailable Value: 1 Key : Hypervisor.Flags.AsyncMemoryHint Value: 0 Key : Hypervisor.Flags.CoreSchedulerRequested Value: 0 Key : Hypervisor.Flags.CpuManager Value: 1 Key : Hypervisor.Flags.DeprecateAutoEoi Value: 1 Key : Hypervisor.Flags.DynamicCpuDisabled Value: 1 Key : Hypervisor.Flags.Epf Value: 0 Key : Hypervisor.Flags.ExtendedProcessorMasks Value: 1 Key : Hypervisor.Flags.HardwareMbecAvailable Value: 1 Key : Hypervisor.Flags.MaxBankNumber Value: 0 Key : Hypervisor.Flags.MemoryZeroingControl Value: 0 Key : Hypervisor.Flags.NoExtendedRangeFlush Value: 0 Key : Hypervisor.Flags.NoNonArchCoreSharing Value: 1 Key : Hypervisor.Flags.Phase0InitDone Value: 1 Key : Hypervisor.Flags.PowerSchedulerQos Value: 0 Key : Hypervisor.Flags.RootScheduler Value: 0 Key : Hypervisor.Flags.SynicAvailable Value: 1 Key : Hypervisor.Flags.UseQpcBias Value: 0 Key : Hypervisor.Flags.Value Value: 21631230 Key : Hypervisor.Flags.ValueHex Value: 14a10fe Key : Hypervisor.Flags.VpAssistPage Value: 1 Key : Hypervisor.Flags.VsmAvailable Value: 1 Key : Hypervisor.RootFlags.AccessStats Value: 1 Key : Hypervisor.RootFlags.CrashdumpEnlightened Value: 1 Key : Hypervisor.RootFlags.CreateVirtualProcessor Value: 1 Key : Hypervisor.RootFlags.DisableHyperthreading Value: 0 Key : Hypervisor.RootFlags.HostTimelineSync Value: 1 Key : Hypervisor.RootFlags.HypervisorDebuggingEnabled Value: 0 Key : Hypervisor.RootFlags.IsHyperV Value: 1 Key : Hypervisor.RootFlags.LivedumpEnlightened Value: 1 Key : Hypervisor.RootFlags.MapDeviceInterrupt Value: 1 Key : Hypervisor.RootFlags.MceEnlightened Value: 1 Key : Hypervisor.RootFlags.Nested Value: 0 Key : Hypervisor.RootFlags.StartLogicalProcessor Value: 1 Key : Hypervisor.RootFlags.Value Value: 1015 Key : Hypervisor.RootFlags.ValueHex Value: 3f7 Key : WER.OS.Branch Value: ni_release Key : WER.OS.Version Value: 10.0.22621.1 BUGCHECK_CODE: a BUGCHECK_P1: ffff8089a2e40ff8 BUGCHECK_P2: 2 BUGCHECK_P3: 1 BUGCHECK_P4: fffff80265872227 FILE_IN_CAB: 041524-31375-01.dmp TAG_NOT_DEFINED_202b: *** Unknown TAG in analysis list 202b WRITE_ADDRESS: fffff802661344a8: Unable to get MiVisibleState Unable to get NonPagedPoolStart Unable to get NonPagedPoolEnd Unable to get PagedPoolStart Unable to get PagedPoolEnd unable to get nt!MmSpecialPagesInUse ffff8089a2e40ff8 BLACKBOXBSD: 1 (!blackboxbsd) BLACKBOXNTFS: 1 (!blackboxntfs) BLACKBOXPNP: 1 (!blackboxpnp) BLACKBOXWINLOGON: 1 CUSTOMER_CRASH_COUNT: 1 PROCESS_NAME: System TRAP_FRAME: ffffa38a491bf5b0 -- (.trap 0xffffa38a491bf5b0) NOTE: The trap frame does not contain all registers. Some register values may be zeroed or incorrect. rax=ffffa38a491bf778 rbx=0000000000000000 rcx=ffffa38a491bf900 rdx=ffffa38a491bf900 rsi=0000000000000000 rdi=0000000000000000 rip=fffff80265872227 rsp=ffffa38a491bf740 rbp=0000000000000000 r8=ffff8089a2e40ff8 r9=0000000000000000 r10=0000000000000018 r11=ffffa38a491befe0 r12=0000000000000000 r13=0000000000000000 r14=0000000000000000 r15=0000000000000000 iopl=0 nv up ei pl nz na po nc nt!KiAcquireQueuedSpinLockInstrumented+0x59: fffff802`65872227 488716 xchg rdx,qword ptr [rsi] ds:00000000`00000000=???????????????? Resetting default scope STACK_TEXT: ffffa38a`491bf468 fffff802`65846269 : 00000000`0000000a ffff8089`a2e40ff8 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx ffffa38a`491bf470 fffff802`65841705 : ffffa38a`491b9000 ffffa38a`491c0000 00000000`00000000 ffffa38a`491bf540 : nt!KiBugCheckDispatch+0x69 ffffa38a`491bf5b0 fffff802`65872227 : ffff8089`a2e40ff8 fffff802`65704902 00000000`00000004 ffffa38a`491bf7b0 : nt!KiPageFault+0x485 ffffa38a`491bf740 fffff802`658625d5 : ffff8088`fa6bd710 ffffa38a`491bf900 ffff8088`fa6bd710 ffff8088`fa6bd6f0 : nt!KiAcquireQueuedSpinLockInstrumented+0x59 ffffa38a`491bf780 fffff802`659f8c77 : fffff802`65ed6271 ffff8088`fa6aec70 00000000`00000000 fffff802`65eebdfb : nt!KeAcquireInStackQueuedSpinLock+0x152465 ffffa38a`491bf7b0 fffff802`65eeb247 : ffff8088`fa6aec70 ffffa38a`491bf919 ffff8089`a2e40ff8 ffffa38a`491bf900 : nt!DifKeAcquireInStackQueuedSpinLockWrapper+0xc7 ffffa38a`491bf800 fffff802`65ed6271 : 00000000`00000000 ffff8089`a2e40f80 fffff802`bb8c2345 ffffa38a`491bf8d0 : nt!VerifierKeAcquireInStackQueuedSpinLockCommon+0x67 ffffa38a`491bf830 fffff802`bb8c2385 : 00000000`00000000 ffffa38a`491bf919 ffff8089`a2e40f80 00000000`0a1dee56 : nt!VerifierKeAcquireInStackQueuedSpinLock+0x11 ffffa38a`491bf860 00000000`00000000 : ffffa38a`491bf919 ffff8089`a2e40f80 00000000`0a1dee56 00000000`00000000 : KfeCo11X64+0x2385 SYMBOL_NAME: KfeCo11X64+2385 MODULE_NAME: KfeCo11X64 IMAGE_NAME: KfeCo11X64.sys STACK_COMMAND: .cxr; .ecxr ; kb BUCKET_ID_FUNC_OFFSET: 2385 FAILURE_BUCKET_ID: AV_VRF_KfeCo11X64!unknown_function OS_VERSION: 10.0.22621.1 BUILDLAB_STR: ni_release OSPLATFORM_TYPE: x64 OSNAME: Windows 10 FAILURE_ID_HASH: {a8dd5be4-b28a-4e52-c33f-ed40455b8b0f} Followup: MachineOwner


 Quote
Quote