New
#21
Play around with windows firewall. You should easily be able to setup a new rule to block connections to the site/ip if it's still trying to redirect you.
Play around with windows firewall. You should easily be able to setup a new rule to block connections to the site/ip if it's still trying to redirect you.
After deleting that registry key, my proxy settings have stayed default. Today I saw a blank command prompt window open for a second and then Chrome was closed. I opened Chrome settings and saw this message: Chrome detected that some of your settings were corrupted by another program and reset them to their original defaults.
Your system still running fine? I did run HitmanPro but it only found cookies on my system. What did it find on yours?
Out of curiosity, have any of you tried a "rescue disc" yet? Several AV's offer them for those tough to clean viruses.
I usually recommend comodo rescue disk but I'm sure almost any AV offers them.
Comodo Rescue Disk for Windows, Download Rescue Disk Software
I am also having this EXACT problem. I have the same registry key listed above and cleared it just now (thanks, this is the only thing I have missed so far), otherwise I have run all the suggested fixes and tools to no avail. Glad I found this thread and that I am not the only one with the issue. I will update on the status of what happens with mine.
I spent the better part of my afternoon the other day trying to get these rescue disks to work. They are a real pain in the butt. Could not get Kaspersky to run at all. I got Comodo to work finally using Yumi and did a full scan of my system, found nothing. I also ran a full scan with Spybot on monday and it found some minor stuff, probably unrelated. My only issue now is that sometimes Chrome will be closed when I come back to my computer. One time I witnessed it happening where a blank command line window opened and Chrome closed. I would love to delete the program that's causing that to happen
Please download and run ADWCleaner. There is a way to save the scan so you can post it here for me (can't remember the steps exactly, but you'll be able to figure it out easily) - do this BEFORE cleaning. ADWCleaner is a powerful program and sometimes it will flag things for deletion that you don't want deleted. So, I'd like to have a look at the scan results before you do any cleaning.
EDIT: Click on the REPORT button after running the scan and post that logfile here in the thread (not as an attachment).
I ran ADWcleaner several days ago. It only found cookies, I think. Pretty sure I fixed everything it found. I found the logfile from that. Not sure what Report button you are talking about? Here is the log:
# AdwCleaner v5.025 - Logfile created 13/12/2015 at 12:24:11
# Updated 13/12/2015 by Xplode
# Database : 2015-12-13.2 [Server]
# Operating system : Windows 10 Pro (x64)
# Username : Michael - MOTHERSHIP
# Running from : D:\Michael\Downloads\adwcleaner_5.025.exe
# Option : Cleaning
# Support : Forum - ToolsLib
***** [ Services ] *****
***** [ Folders ] *****
[-] Folder Deleted : C:\Program Files\Common Files\Speedbit
[-] Folder Deleted : C:\ProgramData\Speedbit
[-] Folder Deleted : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Extensions\pbjikboenpfhbbejgkoklgkhjpfogcam
[-] Folder Deleted : C:\Users\Michael\AppData\Roaming\Speedbit
***** [ Files ] *****
[-] File Deleted : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_pbjikboenpfhbbejgkoklgkhjpfogcam_0.localstorage
[-] File Deleted : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_pbjikboenpfhbbejgkoklgkhjpfogcam_0.localstorage-journal
[-] File Deleted : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\pbjikboenpfhbbejgkoklgkhjpfogcam
***** [ DLLs ] *****
***** [ Shortcuts ] *****
***** [ Scheduled tasks ] *****
***** [ Registry ] *****
[-] Key Deleted : HKCU\Software\Classes\CLSID\{AD4409E5-23C2-412B-849D-8FC0635B4073}
[-] Key Deleted : HKCU\Software\Classes\CLSID\{AEE9D70C-6C9E-4B27-9F2C-8F14E95BEEF6}
[-] Key Deleted : HKCU\Software\Classes\CLSID\{DD20920E-515A-4342-85E3-FC9A9FDA55C2}
[-] Key Deleted : HKCU\Software\Classes\CLSID\{92FDEF05-B35E-4806-B87F-8B66AB649997}
[-] Key Deleted : HKCU\Software\Classes\CLSID\{9F0BF664-B611-4C53-AEEA-FDBFCE6E3CA3}
[-] Key Deleted : HKCU\Software\Classes\CLSID\{A8BD93E8-F6AE-4F02-828D-DE47FEC4D375}
[-] Key Deleted : HKLM\SOFTWARE\Classes\CLSID\{82351441-9094-11D1-A24B-00A0C932C7DF}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{0DC81A74-1FBD-4EF6-82B2-DE3FA05E8233}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{1B26E4A2-7F09-4365-9AB8-13E6891E42CB}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{21402197-BB5B-476C-AA1D-3FFED8ED813A}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{42E8D680-A18B-4CAA-ACE0-18EA05E4A056}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{454A4044-16EC-4D64-9069-C5B8832B7B55}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{4FEB1BAD-35AD-4A08-B6EC-E6D832F1ED4D}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{8F2B3016-17D4-447A-B207-FFA8957A834A}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{E66B63B0-49F8-47E3-A9BA-799287B59E87}
[-] Key Deleted : HKLM\SOFTWARE\Classes\Interface\{F8FA5B48-B7A2-4BC6-8389-9587643A4660}
[-] Key Deleted : HKLM\SOFTWARE\Classes\TypeLib\{82351433-9094-11D1-A24B-00A0C932C7DF}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{0DC81A74-1FBD-4EF6-82B2-DE3FA05E8233}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{1B26E4A2-7F09-4365-9AB8-13E6891E42CB}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{21402197-BB5B-476C-AA1D-3FFED8ED813A}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{42E8D680-A18B-4CAA-ACE0-18EA05E4A056}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{454A4044-16EC-4D64-9069-C5B8832B7B55}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{4FEB1BAD-35AD-4A08-B6EC-E6D832F1ED4D}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{8F2B3016-17D4-447A-B207-FFA8957A834A}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{E66B63B0-49F8-47E3-A9BA-799287B59E87}
[-] Key Deleted : [x64] HKLM\SOFTWARE\Classes\Interface\{F8FA5B48-B7A2-4BC6-8389-9587643A4660}
[-] Key Deleted : HKCU\Software\SpeedBit
[-] Key Deleted : HKCU\Software\Online video player
***** [ Web browsers ] *****
[-] [C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Secure Preferences] [Extension] Deleted : pbjikboenpfhbbejgkoklgkhjpfogcam
[-] [C:\Users\nancy\AppData\Local\Google\Chrome\User Data\Default\Web Data] [Search Provider] Deleted : aol.com
[-] [C:\Users\nancy\AppData\Local\Google\Chrome\User Data\Default\Web Data] [Search Provider] Deleted : ask.com
*************************
:: "Tracing" keys removed
:: Winsock settings cleared
########## EOF - C:\AdwCleaner\AdwCleaner[C1].txt - [4226 bytes] ##########
Okay, let's try this:
Uninstall all Toolbars on the system. (all users)
Uninstall all torrenting/P2P file sharing programs.
Uninstall all downloader programs.
Run RKILL - post the log. (RKILL will stop all malicious and suspect running items, reset hosts, etc. It is temporary. Anything that RKILL does is undone by a reboot.)
Run ADWCleaner again and post the new log here.
Run JRT
Reset all browsers on the system...Reset Edge browser
Flush DNS
Set your network adapter(s) to Open DNS servers:
IPv4 = 208.67.222.222 and 208.67.220.220
IPv6 = 2620:0:ccc::2 and 2620:0:ccd::2
Reboot the computer.
Run RKILL again. Advise if anything is found on this run (check the log).
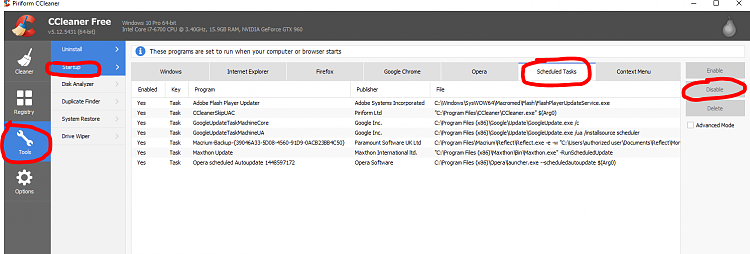
Open Ccleaner to the TOOLS menu on the left and go to STARTUP ITEMS. Post a screenshot of the Google Chrome tab and the Scheduled Tasks tab.
# AdwCleaner v5.025 - Logfile created 17/12/2015 at 21:07:05
# Updated 13/12/2015 by Xplode
# Database : 2015-12-13.2 [Server]
# Operating system : Windows 10 Pro (x64)
# Username : Michael - MOTHERSHIP
# Running from : D:\Michael\Downloads\adwcleaner_5.025 (2).exe
# Option : Scan
# Support : Forum - ToolsLib
***** [ Services ] *****
***** [ Folders ] *****
Folder Found : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Extensions\pbjikboenpfhbbejgkoklgkhjpfogcam
***** [ Files ] *****
File Found : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_pbjikboenpfhbbejgkoklgkhjpfogcam_0.localstorage
File Found : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_pbjikboenpfhbbejgkoklgkhjpfogcam_0.localstorage-journal
File Found : C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\pbjikboenpfhbbejgkoklgkhjpfogcam
***** [ DLL ] *****
***** [ Shortcuts ] *****
***** [ Scheduled tasks ] *****
***** [ Registry ] *****
***** [ Web browsers ] *****
[C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Secure Preferences] [Extension] Found : pbjikboenpfhbbejgkoklgkhjpfogcam
########## EOF - C:\AdwCleaner\AdwCleaner[S4].txt - [1288 bytes] ##########
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Junkware Removal Tool (JRT) by Malwarebytes
Version: 8.0.1 (11.24.2015)
Operating System: Windows 10 Pro x64
Ran by Michael (Administrator) on Thu 12/17/2015 at 21:08:18.64
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
File System: 12
Successfully deleted: C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Extensions\ajpgkpeckebdhofmmjfgcjjiiejpodla (Folder)
Successfully deleted: C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Extensions\lbfehkoinhhcknnbdgnnmjhiladcgbol (Folder)
Successfully deleted: C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Extensions\pbjikboenpfhbbejgkoklgkhjpfogcam (Folder)
Successfully deleted: C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_ajpgkpeckebdhofmmjfgcjjiiejpodla_0.localstorage-journal (File)
Successfully deleted: C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_ajpgkpeckebdhofmmjfgcjjiiejpodla_0.localstorage (File)
Successfully deleted: C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_pbjikboenpfhbbejgkoklgkhjpfogcam_0.localstorage-journal (File)
Successfully deleted: C:\Users\Michael\AppData\Local\Google\Chrome\User Data\Default\Local Storage\chrome-extension_pbjikboenpfhbbejgkoklgkhjpfogcam_0.localstorage (File)
Successfully deleted: C:\Users\Michael\AppData\Roaming\Mozilla\Firefox\Profiles\37lpeheh.default\extensions\staged (Folder)
Successfully deleted: C:\WINDOWS\SysWOW64\REN25DB.tmp (File)
Successfully deleted: C:\WINDOWS\SysWOW64\REN5382.tmp (File)
Successfully deleted: C:\WINDOWS\SysWOW64\REN62C0.tmp (File)
Successfully deleted: C:\WINDOWS\SysWOW64\RENAAF3.tmp (File)
Deleted the following from C:\Users\Michael\AppData\Roaming\Mozilla\Firefox\Profiles\37lpeheh.default\prefs.js
user_pref(extensions.sovetnik.yandex.statistics.clid.21, 2238478-002);
Registry: 0
----
Chrome startup attached
--- RKILL log here. Couldn't paste here, too long. Nothing significant there though.
Whoa! I have never, in all my years cleaning viruses off computers, seen an RKILL log like that!
Has your computer been running slow at all? It appears as if your entire Windows OS is loaded with reparse junctions that point to nowhere.
These are nothing - video files from ASUSRkill 2.8.3 by Lawrence Abrams (Grinler)
BleepingComputer.com - News, Reviews, and Technical Support
Copyright 2008-2015 BleepingComputer.com
More Information about Rkill can be found at this link:
RKill - What it does and What it Doesnt - A brief introduction to the program - Anti-Virus, Anti-Malware, and Privacy Software
Program started at: 12/17/2015 09:22:09 PM in x64 mode.
Windows Version: Windows 10 Pro
Checking for Windows services to stop:
* No malware services found to stop.
Checking for processes to terminate:
* C:\Windows\SysWOW64\HsMgr.exe (PID: 7564) [WD-HEUR]
* C:\Windows\System\HsMgr64.exe (PID: 7892) [WD-HEUR]
2 proccesses terminated!
This legitimate dll file has a reparse point to nowhere - that is suspicious, and why I ask if your computer was running slow. Zeroaccess is part of a botnet which either runs clickfraud or bitcoin mining.Checking Registry for malware related settings:
* No issues found in the Registry.
Resetting .EXE, .COM, & .BAT associations in the Windows Registry.
Performing miscellaneous checks:
* ALERT: ZEROACCESS Reparse Point/Junction found!
* C:\Program Files\Windows Defender\mpuxhostproxy.dll => <Unknown Target> [File]
And the list goes on and on for reparse points-thousands of them. Honestly, I've never seen anything like this.* Reparse Point/Junctions Found (These may be legitimate)!
* C:\WINDOWS\AppPatch\AcGenral.dll => <Unknown Target> [File]
* C:\WINDOWS\AppPatch\AcRes.dll => <Unknown Target> [File]
* C:\WINDOWS\AppPatch\AcSpecfc.dll => <Unknown Target> [File]....
You've got a major problem with your hosts file.Checking HOSTS File:
* HOSTS file entries found:
127.0.0.1 209.34.83.73:443
127.0.0.1 209.34.83.73:43
127.0.0.1 209.34.83.73
127.0.0.1 209.34.83.67:443
127.0.0.1 209.34.83.67:43
127.0.0.1 209.34.83.67
127.0.0.1 ood.opsource.net
127.0.0.1 199.7.52.190:80
127.0.0.1 199.7.52.190
127.0.0.1 OCSP.SPO1.VERISIGN.COM
127.0.0.1 199.7.54.72:80
127.0.0.1 199.7.54.72
127.0.0.1 192.150.14.69
127.0.0.1 192.150.18.101
127.0.0.1 192.150.18.108
127.0.0.1 192.150.22.40
127.0.0.1 192.150.8.100
127.0.0.1 192.150.8.118
127.0.0.1 209-34-83-73.ood.opsource.net
127.0.0.1 3dns-1.adobe.com
20 out of 87 HOSTS entries shown.
Please review HOSTS file for further entries.
I will tell you what I would do at this point: either do a clean install, completely formatting your hard drive, or post for help at Bleeping Computer, to see if they are able to sort things.