New
#1
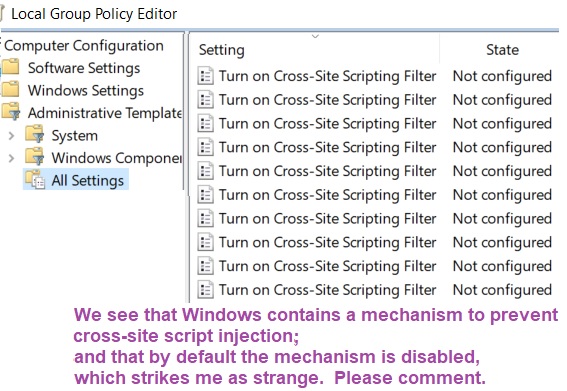
script injection allowed by default
-
-
New #2
Because cross site or XSS is to do with Javascript where in the case of blocking these things can mean broken webpages or webpages that don't display properly. You need to know how to navigate around if you were to enable XSS prevention like this and therefore it does not make sense to have these enabled by default as the generic computer user would not know what to do.
Basically the web browser cannot determine if JS is legit or not well it cannot do so very well in some contexts and its easy for people to do bad things with JS, This is what XSS blocking is about.
These policy only apply to Internet Explorer, and maybe Edge not sure on Edge though. So if you don't use these then its not an issue.
- - - Updated - - -
X-XSS-Protection - HTTP | MDN
-
New #3
Furthermore, and contrary to what you wrote, we do not "see ... that by default the mechanism is disabled".
All we see is that Group policy has not been used to alter the mechanism. That is all that "Not configured" means.
All the best,
Denis
-
New #4
It is also an older system that is vulnerable. Content-Security-Policy is the newer better version.
-
New #5
-
-
New #7
I believe it. (even had thought of the possibility that it might be that way)
What about vice-versa, an enabled policy that contradicts a registry setting -- does the setting change accordingly?
-
New #8
If you set the policy up after having fiddled with the Registry then the policy settings will be written over whatever you had done before.
Denis
-
Related Discussions


 Quote
Quote