New
#1
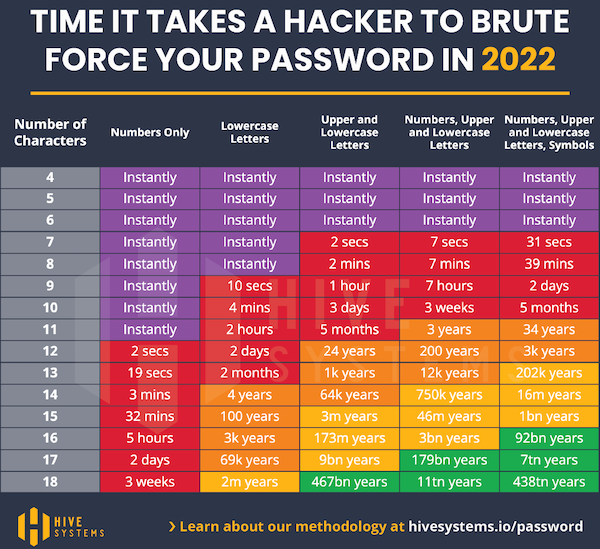
Brute force time chart
-
-
-
New #3
I just typed this into the password tester.... it said it would take 10000+ centuries to crack.
bner-vgf098134y-t7819u34h-gf98h3er480gj3r490t`gj=3954jgf`i980234njfi9023jm-fo
This is apparently, also a great password taking 10000+ centuries to crack...
supercalifragilisticexpialidocious
-
-
-
New #6
-
New #7
I can't really explain it very well.
By way of analogy... let's say you wanted to find the fastest route between NY and SF, and you were starting in NY.
Already you know, you aren't gonna want roads that go North or South or East, so you just eliminated 75% of the possible roads.
The same with passwords. Let's just say that all passwords were required to have characters including...
uppercase, lower case, numbers, and symbols. Already you can eliminate any passwords that are ALL...
numbers, or lower case, or upper case or symbols, because the requirements were for some of each.
Then let's say all the possible passwords have to be created on a US English keyboard.
You can then eliminate all non-US English characters as well.
Then let's add in a requirement that all passwords have to be eight characters or more.
You can then eliminate all passwords that are less than eight characters.
The point is... a brute force tool by itself is fast. BUT, it's that much "faster", if humans can come along and say you don't have to "try" for... this and this and this and this... etc.
There will also be many hash formulae that can be eliminated as well.
And there won't be THAT many possible hash formulae to begin with.
Really short version...
Brute force with some human grey matter direction, will be much faster than "just" brute force.
Let's say you're a hacker and you want to brute force everyone's password at... Bank X.
When a person goes to make a password at Bank X, there will be certain password requirements.
So right there, you can instruct your brute force program to "skip" searching for all passwords that don't fit those password requirements. And I'm sure there are more "eliminations" that can be made.
-
New #8
-
-
New #9
OK - but I still don't get it - by what mechanism can a hacker find two // in a row?
-
Related Discussions


 Quote
Quote

