New
#1
Wow - very pervasive/aggressive "malware", can't solve
Folks - I have one single machine with the most pervasive, confounding "malware" effects I've ever dealt with in 30 years of work in tech. (And I even wrote some viruses and Trojans myself in everything from assembly to C++ in my early days doing formal study of operating systems.)
I also can't find out anything specific about a similar infection type here or on other forums.
This is a personal HP Pavilion X360 exclusively bought and provisioned for my daughter to use for virtual school work on our home network.
Initial behavior:
- When any version of Windows 10/11 is clean-installed after all partitions are deleted, Windows behaves fine when offline - I can manually install any number of KBs, BIOS updates, OEM drivers, etc. and I've tried maybe 5 different Windows ISOs from pre-21H1 through Win11 22000.71
- When initially offline, Malwarebytes / Emsisoft report no malware - even scanning for rootkits, even scanning with direct HD access
- When initially offline, SFC reports no integrity violations & chkdsk reports no errors
As mentioned above, BIOS update is applied - Bios name/revision match HP's latest specs.
I then pause Windows Updates and join a network.
The following behavior makes ZERO difference how many / which users / built-in Administrator account are set up on the machine.
Malware behavior:
- Within minutes of joining any network, User Account Control asks to be turned off and system restarted (similar to UAC is consistently turning itself off.). NOTE - I have manually changed computer name / static IPs/DNS settings repeatedly during each clean install process, so this is occurring regardless of the computer's specific IP when it joins.
- At this point, Malwarebytes reports Task Manager has been disabled; CMD has been disabled; Registry tools have been disabled - Emergency Kit reports the same findings. Neither tool reports specific malware.
- Upon next reboot, I get the old "user profile service failed the sign-in" - no restoration methods work from here on out
So...some kind of a RAT?
The only other thing I could think of is if it's not really malware, but some failed attempt by HP to install another driver, but you'd think it'd go through the correct chain of command.
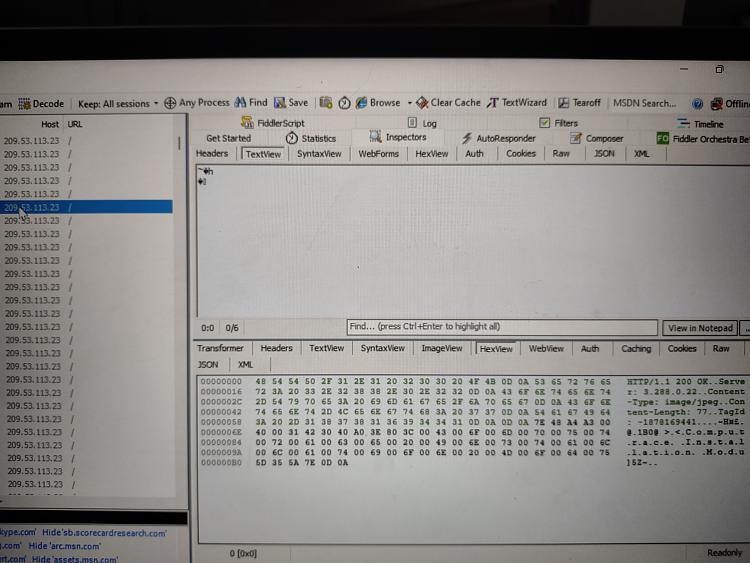
I'm thinking of installing Fiddler right away too during the offline process and watching for what traffic is happening.


 Quote
Quote