New
#21
Clear Windows Security Center (Defender) Protection History
-
-
-
New #23
no matter what I do it's still there . Let's see if they will erase after a month
-
New #24
M$ has made it more difficult to delete the the Service folder so I worked out a new simple method.
Code:#1 Restart in safe mode. #2 In elevated command prompt run "takeown /f "C:\ProgramData\Microsoft\Windows Defender\Scans\History\Service" /r" (without the outer quotes) #3 Delete folder "Service" in C:\ProgramData\Microsoft\Windows Defender\Scans\History #4 Restart
-
New #25
Run this script ClearDefenderHistory.bat to safely stop Defender protections, clear the history files, and restart protection. It's a wrapper to a PowerShell script that creates a temporary scheduled task, and runs as TrustedInstaller.
ClearDefenderHistory.bat
This is a much better approach than taking ownership of Defender folders, which is a security hole since if you can delete files, so does malware running as you. The script waits for the task to complete (or times out), and removes the task. If you're not already Administrator, it will ask for permissions.Last edited by Brink; 07 Mar 2024 at 13:58.
-
New #26
As the only folder affected "C:\ProgramData\Microsoft\Windows Defender\Scans\History\Service" is deleted and then recreated by the system with the same attributes upon reboot, there is no security issue.
I do like single click solutions though.
Q: Are those screenshots from Win11? They look very annoying, M$ telling you your privacy is a security issue. I will move to 11 from 10 when 10 reaches EOL but not before.
-
New #27
I wrote the script on 11, but it works the same. When I see folks doing take ownership, a few beginners get the wrong message and start experimenting on other folders. Then you'll see a thread where they're asking to fix their messed up Windows.
If there's a non-zero risk of messing up, it's better to provide a scripted solution that does it by the book.
-
New #28
I use , DefenderUI
Turn off Tamper Protection in Defender and close it.
Select 'Clear and repair Protection History' in DefenderUI and reboot.
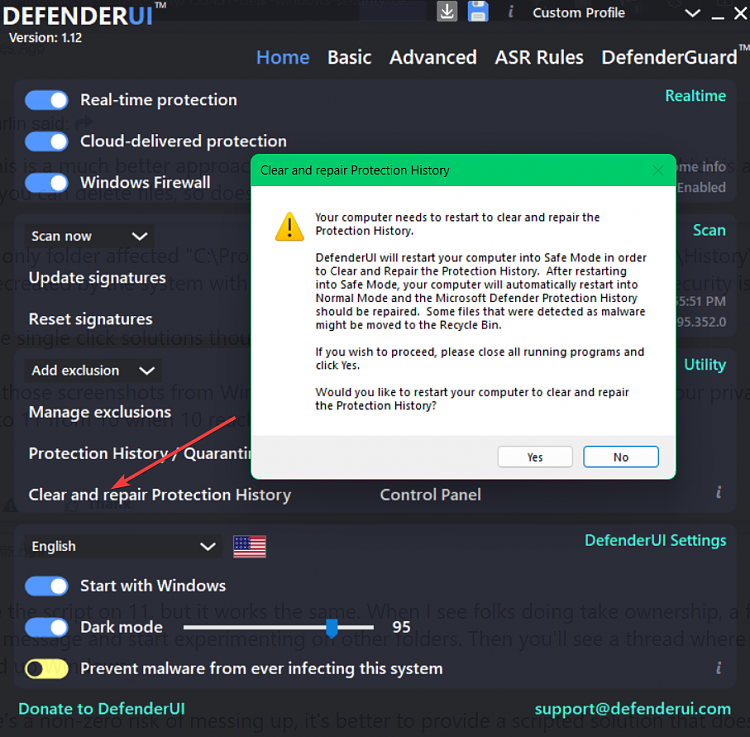
Turn on Tamper Protection.
-
-
New #29
Bless you! This is the only solution that works 100%.
My Detections.log file was locked in use by the WinDefend service, so I couldn't delete it. In theory, I should have been able to open a Cmd prompt as TrustedInstaller, stop the service and delete the file. I tried doing that with PowerRun, but still couldn't stop the service. Rather than spend more time fussing with it, I took a look at your script, saw that it made sense, and ran it. Bingo!
The reason I needed to delete the history is that it was causing a continued false positive. That is, I made a new utility, tested the download from my GitHub page and, as expected, it detected it as a virus. I then submitted a false positive report to the Defender team and they agreed and updated their definitions. Testing on another computer, with the definitions up to date, the utility then downloaded without any issue. However, on my main machine, with updated definitions, even after rebooting, it continued to detect the file as a virus. I knew from past experience that I needed to clear Defender's history to fix the issue. Your batch file made that very easy and will come in so handy when this happens again.
Thank you!! 🤗
P.S. You should give this script it's own GitHub page. I'm sure many others would benefit. Or, if it's okay with you, I can post it on my page (with all credit to you in the readme).
-
New #30
@LesFerch, go ahead and repost it on your GitHub if that will increase visibility.
I borrowed part of another script (referenced in the comments) to do the TI elevation. While I've seen other elevation hacks, this one is the most clear in explaining how it does the actual work. You can use it for writing other privileged scripts.
Related Discussions


 Quote
Quote