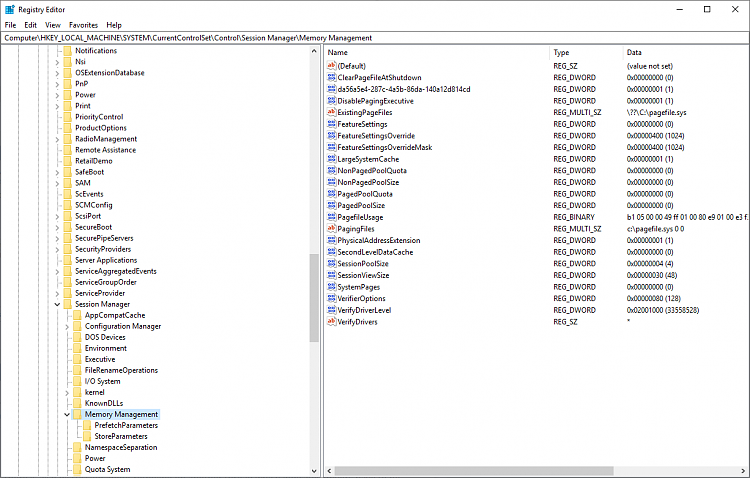
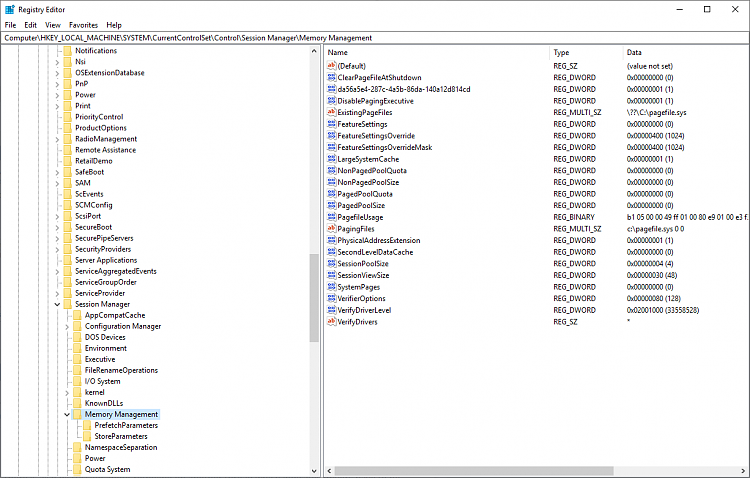
I'm having an odd issue where BTIKernelRetpolineEnabled reports as true, but BTIKernelImportOptimizationEnabled reports as false, which I didn't even know was possible. I had nothing for the registry entries, and now both are set to 400.
I have the latest microcode patch installed for my processor as well:
Code:
CPU-Info Version 2.1 © 2019 Dimitri Delopoulos
Computer Model : MS-7885
Computer Name : Z
Processor Type : Central Processor
Manufacturer : GenuineIntel
CPU Family : Intel(R) Xeon(TM)
CPU Architecture : x64
Name : Intel(R) Core(TM) i7-5820K CPU @ 3.30GHz
Description : Intel64 Family 6 Model 63 Stepping 2
Number of Cores : 6
Number of Logical Processors : 12
Current Clock Speed : 3301
Socket Designation : SOCKET 0
Upgrade Method : Socket LGA2011-3
CPUID : 000306F2
Display Family : 06H
Display Model : 3FH
Running microcode revision : 0x3D (loaded by UEFI)
UEFI CPU microcode revision : 0x3D
Boot Mode : UEFI
UEFI Version : P.60
UEFI Manufacturer : American Megatrends Inc.
UEFI Serial Number : Default string
UEFI Release Date : 2018-06-14 (273 days ago)
Here's the full output of Get-SpeculationControlSettings:
Code:
PS C:\WINDOWS\system32> Get-SpeculationControlSettings
For more information about the output below, please refer to https://support.microsoft.com/en-in/help/4074629
Speculation control settings for CVE-2017-5715 [branch target injection]
Hardware support for branch target injection mitigation is present: True
Windows OS support for branch target injection mitigation is present: True
Windows OS support for branch target injection mitigation is enabled: True
Speculation control settings for CVE-2017-5754 [rogue data cache load]
Hardware requires kernel VA shadowing: True
Windows OS support for kernel VA shadow is present: True
Windows OS support for kernel VA shadow is enabled: True
Windows OS support for PCID performance optimization is enabled: True [not required for security]
Speculation control settings for CVE-2018-3639 [speculative store bypass]
Hardware is vulnerable to speculative store bypass: True
Hardware support for speculative store bypass disable is present: True
Windows OS support for speculative store bypass disable is present: True
Windows OS support for speculative store bypass disable is enabled system-wide: False
Speculation control settings for CVE-2018-3620 [L1 terminal fault]
Hardware is vulnerable to L1 terminal fault: True
Windows OS support for L1 terminal fault mitigation is present: True
Windows OS support for L1 terminal fault mitigation is enabled: True
BTIHardwarePresent : True
BTIWindowsSupportPresent : True
BTIWindowsSupportEnabled : True
BTIDisabledBySystemPolicy : False
BTIDisabledByNoHardwareSupport : False
BTIKernelRetpolineEnabled : True
BTIKernelImportOptimizationEnabled : False
KVAShadowRequired : True
KVAShadowWindowsSupportPresent : True
KVAShadowWindowsSupportEnabled : True
KVAShadowPcidEnabled : True
SSBDWindowsSupportPresent : True
SSBDHardwareVulnerable : True
SSBDHardwarePresent : True
SSBDWindowsSupportEnabledSystemWide : False
L1TFHardwareVulnerable : True
L1TFWindowsSupportPresent : True
L1TFWindowsSupportEnabled : True
L1TFInvalidPteBit : 45
L1DFlushSupported : True
If anybody has any thoughts, I would appreciate it!



 Quote
Quote